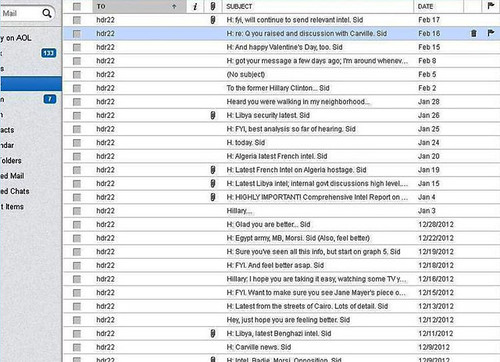
So this Hillary Clinton’s e-mail leak case has been a pretty interesting phenomena to observe and has been going on since last month, we didn’t really cover it as well it mostly concerns US politics – not a huge area of interest for most.
But it’s getting more and more interesting, there was a report that 32,000 of Hillary Clinton’s Email for auction to the highest bidder.
But it was rather unsubstantiated. Now it’s getting more and more interesting, seeing as though Hillary used a private e-mail server “for convenience” and this server also had VNC and RDP open to the INTERNET. Yah..
It also includes her using the same e-mail, yes a state department server technically, for personal e-mails.
Not only did Democratic Party presidential hopeful Hillary Clinton run her own email server while at the State Department: someone, presumably her friendly local sysadmin, decided it needed remote desktop protocol (RDP) and desktop sharing code virtual network computing (VNC) exposed to the Internet.
The folks at Associated Press were alerted to the situation by a Serbian geek the newswire hasn’t named, but who ran bulk port-scans that happened to include Hillary’s email server.
The scans came from the anonymous researcher who in 2013 published the white-botnet-driven “Internet census”, AP says.
Scans of a server that identified itself as clintonemail.com in August and December 2012 showed open ports for RDP and VNC. In March 2012, Microsoft warned that RDP was likely to be attacked, and in October of the same year Verizon warned that RDP’s default Port 3389 was among the most-scanned on the Internet.
So yah, apart from running her own e-mail server rather than using government resources or using a more secure, managed e-mail solution like Google Apps, whoever set it up also thought having VNC and RDP open to the Internet was a smart idea.
Or well, more likely they didn’t think about it at all. It was just such a hassle to get into wherever the server was stored, they installed remote access software and enabled it over the public IP.
VPN? What?
The researcher told AP the server also presented VNC to the Internet at large.
The State Department at the time required a waiver for any of its own techs to use remote access tools for systems administration, all the way down to unclassified servers, the AP notes.
There’s also a suggestion that a Web server – probably bundled with whichever operating system distribution clintonemail.com ran – was running, although not in use.
The Internet Census port-scan showed two other devices that had open ports, but those aren’t identified by the newswire. Presumably one of them was a broadband modem – still leaving one mystery device to be identified.
Another interesting story to note is that all the e-mails were backed up to the cloud using a service called Datto Inc:
Unbeknownst to Clinton, IT firm had emails stored on cloud; now in FBI’s hands
And I wonder if their waivers were signed? I somehow doubt protocol was followed in this case, as using a state funded e-mail server for personal e-mails is probably very much against due process.
Now this was a while back, the actual occurrence being in 2012 – but I guess it’s rising back up again now with Hillary vying for the presidency.
Source: The Register
