LiMe is a Loadable Kernel Module (LKM) Linux memory extractor which allows for volatile memory acquisition from Linux and Linux-based devices, such as Android. This makes LiME unique as it is the first tool that allows for full memory captures on Android devices. It also minimizes its interaction between user and kernel space processes during acquisition, which allows it to produce memory captures that are more forensically sound than those of other tools designed for Linux memory acquisition.
Features
- Full Android memory acquisition
- Acquisition over network interface
- Minimal process footprint
Usage
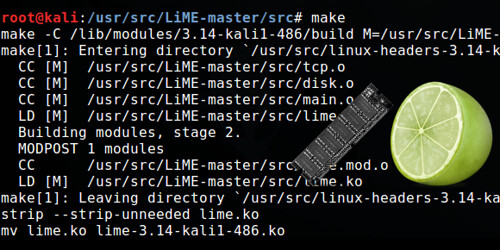
Detailed documentation on LiME’s usage and internals can be found in the “doc” directory of the project. LiME utilizes the insmod command to load the module, passing required arguments for its execution.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 |
insmod ./lime.ko "path=<outfile | tcp:<port>> format=<raw|padded|lime> [dio=<0|1>]" path (required): outfile ~ name of file to write to on local system (SD Card) tcp:port ~ network port to communicate over format (required): raw ~ concatenates all System RAM ranges padded ~ pads all non-System RAM ranges with 0s lime ~ each range prepended with fixed-size header containing address space info dio (optional): 1 ~ attempt to enable Direct IO 0 ~ default, do not attempt Direct IO localhostonly (optional): 1 restricts the tcp to only listen on localhost, 0 binds on all interfaces (default) |
Examples
In this example we use adb to load LiME and then start it with acquisition performed over the network:
|
1 2 3 4 5 |
$ adb push lime.ko /sdcard/lime.ko $ adb forward tcp:4444 tcp:4444 $ adb shell $ su # insmod /sdcard/lime.ko "path=tcp:4444 format=lime" |
Now on the host machine, we can establish the connection and acquire memory using netcat
|
1 |
$ nc localhost 4444 > ram.lime |
Acquiring to sdcard
|
1 |
# insmod /sdcard/lime.ko "path=/sdcard/ram.lime format=lime" |
You can download LiMe v1.7.2 here:
Or read more here.
