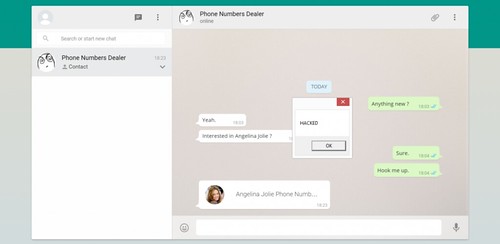
So it seems there was a lot of noise about the WhatsApp Web vCard Vulnerability with over 200 Million people using the desktop version of WhatsApp – it’s a fairly large cache of users to go after.
Disclosed by Check Point security, the vulnerability is exploited by sending a vCard contact containing malicious code to a WhatsApp Web user.
The vulnerability lies in the improper filtering of contact cards using the popular vCard format, thankfully WhatsApp reacted fairly fast on this.
A vulnerability discovered in WhatsApp Web, the web-based extension of the WhatsApp mobile application, can be exploited by attackers to trick users into executing arbitrary code on their machines.
Discovered by Check Point security researcher Kasif Dekel, the vulnerability can be exploited by simply sending a vCard contact card containing malicious code to a WhatsApp user. As soon as the seemingly innocent vCard is opened in WhatsApp Web, the malicious code in it can run on the target machine.
This vulnerability allows cybercriminals to compromise the affected computer by distributing all types of malware, including ransomware, bots, and remote access tools (RATs), Check Point’s researcher explains.
The underlying issue lies in the improper filtering of contact cards that are sent using the popular ‘vCard’ format. “By manually intercepting and crafting XMPP requests to the WhatsApp servers, it was possible to control the file extension of the contact card file,” the Check Point researcher explained in a blog post.
An attacker can inject a command in the name attribute of the vCard file, separated by the ‘&’ character. Windows automatically tries to run all lines in the file, including the injection line, when the vCard is opened.
The vulnerability is fixed and has been since August 27th, which is rapid considering the vulnerability was only disclosed to them on August 21st. Public disclosure came this week on September 8th.
You can read the full report from Check Point here: WhatsApp “MaliciousCard” Vulnerabilities Allowed Attackers to Compromise Hundreds of Millions of WhatsApp Users
This attack does not require XMPP interception of crafting, due to the fact that anyone can create such a contact with an injected payload, directly on the phone, Check Point notes. As soon as the contact is ready, the attacker only needs to share it through the WhatsApp client to unsuspicious users.
Check Point also explains that WhatsApp failed to validate the vCard format or the contents of the file, and that even an exe file could have been sent this way. Even more, malware could have been attached to a displayed icon, opening a vast world of opportunity for cybercriminals and scammers
Over the past several years, WhatsApp has grown to become one of the popular messaging services on mobile phones, with over 900 million users as of this month, and it has extended to the desktop as well, where it has over 200 million users.
WhatsApp Web provides users with access to all of the messages that they have sent or received, including includes images, videos, audio files, locations and contact cards, and keeps all content synchronized with the phone, so that users can access it on both desktop and mobile devices.
Additionally, the web-based interface allows users to view all of the sent or received attachments, as long as they are accessible through the mobile application, including images, audio and video files, location info, and contact cards.
It’s cute how they tried to come up with a catchy name too like HeartBleed or LogJam – they went with ‘MaliciousCard’.
It’s rather surprising more companies or bad guys aren’t going after messaging services as they have such immense user bases (Over 900 Million for WhatsApp). Or perhaps they are, and there’s a bunch of zero-days out there no one knows about yet. That is very possible.
Source: Security Week
