So it seems like getting rid of Ballmer was the best thing Microsoft has done in years, Satya is definitely pushing them in a much more positive direction with a focus on Azure and open sourcing technology and moves like this OpenSSH on Windows!
A real show of support for open source technology and a commitment to making Windows servers more technologically relevant.
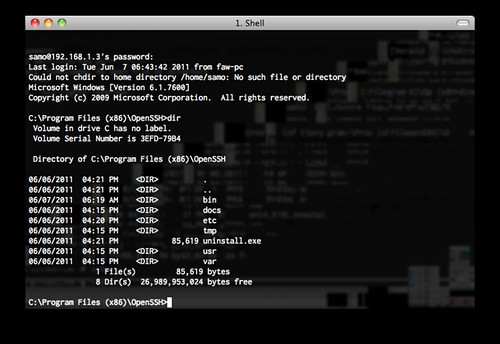
There have long been 3rd integrations with Windows to provide SSH support, but it’s good to finally a see real commitment by Microsoft themselves to do encrypted remote access the right way.
Microsoft has finally decided to add support for SSH to PowerShell, allowing people to log into Windows systems and use software remotely over an encrypted connection.
Users of Linux, the BSDs, and other operating systems, will know all about OpenSSH and its usefulness in connecting machines in a secure way to execute commands and transfer data. And soon Windows PowerShell – the command-line shell and scripting language – can be used over SSH, we’re told.
“The PowerShell team [will] adopt an industry-proven solution while providing tight integration with Windows; a solution that Microsoft will deliver in Windows while working closely with experts across the planet to build it,” wrote Microsoft group software engineering manager Angel Calvo.
“I’m pleased to announce that the PowerShell team will support and contribute to the OpenSSH community.”
PowerShell’s SSH support will allow users to “interoperate between Windows and Linux – both Linux connecting to and managing Windows via SSH and, vice versa, Windows connecting to and managing Linux via SSH.”
This brings in a whole new era of monitoring and automation for Windows DevOps guys, more integration with Linux tools and easier deployment etc as pretty much everything already supports SSH.
In many environments the use of a 3rd party SSH server would be prohibited (against service contracts etc) so the fact it’s going to be ‘officially’ part of Windows going forwards is great.
This isn’t the first time Microsofties have tried to adopt SSH for Windows. Engineers at Redmond giant say they had tried on two separate occasions to allow the secure protocol to be used within Windows, attempts that were struck down by leadership.
Third-party SSH tools have been available on Windows for years, but this announcement is effectively Microsoft’s official endorsement of the open-source technology.
The change in policy has been linked directly to changes at the top of Microsoft – the departure of Steve Ballmer as CEO and the rise of Satya Nadella, a move that MS employees say brought a change in culture and perspective in Redmond.
“Given our changes in leadership and culture, we decided to give it another try and this time, because we are able to show the clear and compelling customer value, the company is very supportive,” Calvo wrote.
“So I want to take a minute and thank all of you in the community who have been clearly and articulately making the case for why and how we should support SSH! Your voices matter and we do listen.”
Well, they listen now that Ballmer is out of the picture.
There’s no time-line for release of this right now, I wonder if it’s something that will come out with Windows 10? Or something they are only just starting to work on now?
Either way it’s definitely a positive move and I hope to see more industry standards infiltrate the Microsoft ecosystem and the era of proprietary technologies for remote control, network stacks and so on die off.
Source: The Register
