Ever find yourself looking for that show-stopper exploit in a Web-app, and forgetting to check out all the low-hanging fruit? That’s initially why the authors created Watcher – a passive web application vulnerability scanner.
For one thing, you don’t want to manually inspect a Web-app for many of these issues (cookie settings, SSL configuration, information leaks, etc), but you still want to find and fix them. Watcher provides this level of security analysis, plus provides hot-spot detection to help pen-testers focus in on the spots that will lead to that show-stopper exploit.
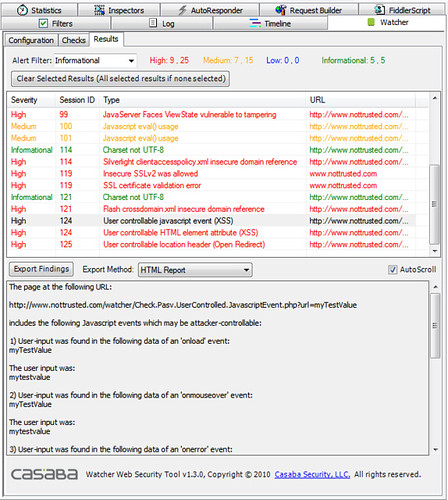
Watcher is a Fiddler add-on which aims to assist penetration testers in passively finding Web-application vulnerabilities. The security field today has several good choices for HTTP proxies which assist auditors and pen-testers. The tool was implemented as a plugin for Fiddler which already provides the proxy framework for HTTP debugging.
Some reasons to use Watcher include:
- Safe for the Cloud and hosting environments. Being passive gives Watcher several advantages – when applications live in the Cloud there’s often a risk that running security testing could damage the shared infrastructure. However, using a passive tool like Watcher ensures that there’s no chance of damaging Cloud-like infrastructure.
- Safe for production environments. Watcher does not attack web-applications with loads of intrusive requests, it doesn’t modify inputs to your application. Unlike crawlers and web-application scanners, Watcher does not generate dangerous traffic. It quietly analyses normal user-interaction and makes educated reports on the security of an application.
- Low overhead, no training. If you’re building web-applications you already have a development and test staff. Fiddler has been valuable to dev and test for years as a general-purpose HTTP debugging proxy. Watcher fits seamlessly into the picture, providing valuable security insight with no special training requirements, dedicated machines, or other resources.
Checks make up the most useful part of Watcher – they provide analysis of the HTTP traffic and reporting of security findings. As someone running the tool you can enable, disable, and configure checks independently. As a developer you can create custom and new checks for private use or to contribute to the public project.
Watcher currently ships with 38 standard checks. A check is defined as one set of logic usually stored in a single source code file. Checks can look for multiple issues, so a single check can end up reporting several separate findings.
The contents below are divided by the categories in which different checks operate. Within each category individual checks have been documented separately.
You can download Watcher here:
Or read more here.
