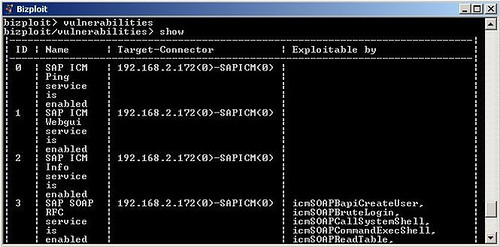
Onapsis Bizploit is an SAP penetration testing framework to assist security professionals in the discovery, exploration, vulnerability assessment and exploitation phases of specialized SAP security assessment. The framework currently ships with many plugins to assess the security of SAP Business Platforms. Additional plugins are available for broader platform support including Oracle.
Nowadays, most organizations which use SAP are going beyond the simple definition of SAP roles and profiles. They have incorporated the technical layer of their SAP platform into their regular risk assessment processes, in order to address the increased threat of cyber-attacks to their business-critical systems.
With Bizploit, you can perform basic analysis of some of the existing technical vulnerabilities affecting your SAP systems, which often pose critical risks to the integrity of the entire platform.
New in v1.50
- New exploits for Management Console.
- New modules for SAProuter.
- New modules for remote execution of RFC Functions.
- Module to detect the CTC Verb Tampering vulnerability.
- Several bug fixes.
You can download Bizploit here (requires registration):
Or read more here.
