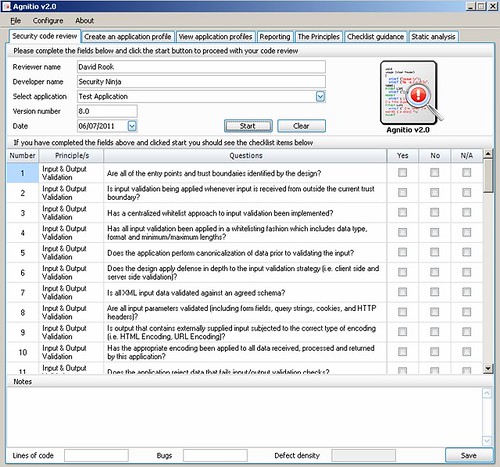
A tool to help developers and security professionals conduct manual security code reviews in a consistent and repeatable way. Agnitio aims to replace the adhoc nature of manual security code review documentation, create an audit trail and reporting.
It hasn’t been updated for a fair while sadly, and v2.1 was released in 2011 – but still it’s a useful tool and a decent update. The last time we wrote about it was when Agnitio v2.0 was released back in August 2011.
The major changes in v2.1 are listed below:
- Windows x64 support
- Automatically decompile Android .apk application to easily analyse the apps source code
- Application profiles now have an application type of either web or mobile which allows only relevant checklist items to be displayed during the security code review
- Create new checklist questions and mark them as web or mobile
- C# and Java rules from the OWASP Code Crawler project have been imported into the Agnitio database and linked to relevant checklist questions
You can download Agnitio v2.1 here:
x64 – Agnitio x64.zip
x86 – Agnitio x86.zip
Or read more here.
