[ad] It was 2008 when the UK government originally proposed disconnecting pirates from the Internet, then a few months later Australia followed suit. The latest is that it’s really going to be legislated and will come into force by April 2010 under the Digital Economy Bill. I’ve noticed this trend picking up lately, a few […]
VPN
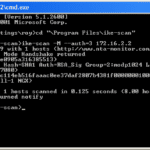
ike-scan – IPsec VPN Scanner & Testing Tool
ike-scan is a command-line IPSec VPN Scanner & Testing Tool for discovering, fingerprinting and testing IPsec VPN systems. It constructs and sends IKE Phase-1 packets to the specified hosts, and displays any responses that are received. IKE is the Internet Key Exchange protocol which is the key exchange and authentication mechanism used by IPsec. Just […]
SSL VPNs and OpenVPN – Part IV
4. Brief How-to …. Creating Multiple clients to Single site tunnels. Example of using PKI to create a client-to-site VPN: For a road warrior or roaming/multiple user scenario, static keys based VPNs don’t scale well. You will need to implement a PKI if you have Hub and Spoke architecture of VPN. From the OpenVPN.net website: […]
SSL VPNs and OpenVPN – Part III
3. Brief How-to ….. OpenVPN and Site-to-Site Tunnels. OpenVPN can be implemented either Site-to-site or client-server model. I will take example configurations of both models. If you want to implement site-to-site configuration, the best way is to use static-keys instead of PKI. Using static keys, you can have your VPN tunnel up and running in […]
SSL VPNs and OpenVPN – Part II
2. Why OpenVPN Here, in this article, I will lay down the emphasis on one important Open-Source SSL VPN software written by James Yonan and contributed by several others, which proposes security without the inherent complexity of IPsec AND using a trusted design of client component and VPN server. Usually VPNs require end points which […]