Following shortly after the .io domain cock-up that left thousands vulnerable to domain hijacking, this week more than 750 domains were jacked via registrar Gandi. Seems like some pretty sloppy administration going on, but that’s how business goes sadly security is still a very much reactive trade. People don’t enable strict controls and audit unless […]
Web Hacking
Web hacking is always the latest headline find web hacking 101, tools, web site hacking, web application hacking and the latest news about website hacking here.
Some examples of web hacking tools are:
- wwwhack 1.9 – wwwhack19.zip Web Hacking Software Free Download
- Wfuzz Download – Web Application Password Cracker
- FLARE – Flash Decompiler to Extract ActionScript
- WebSurgery – Web Application Security Testing Suite
Some examples of web hacking protection are:
OneLogin Hack – Encrypted Data Compromised
The OneLogin hack is blowing up now it seems like whoever got access can also decrypt encrypted customer data which is just about AS BAD as it can get for a password/identity management service. Now I’m a HUGE supporter of password management tools as I’ve mentioned many times here, so anyone who signed up for […]
Microsoft Azure Web Application Firewall (WAF) Launched
Not too long after Amazon launched their cloud protection WAF the Microsoft Azure Web Application Firewall (WAF) has been made generally available in all public Azure DCs. It’s a good move with the majority of websites and services moving into one of the big 3 cloud providers (AWS, Google or Azure) and the vast majority […]
Minion – Mozilla Security Testing Framework
Minion is a security testing framework built by Mozilla to bridge the gap between developers and security testers. To do so, it enables developers to scan with a wide variety of security tools, using a simple HTML-based interface. It consists of three umbrella projects: Minion Frontend, a Python, angular.js, and Bootstrap-based website that provides a […]
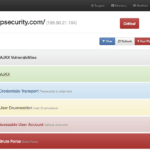
OWASP OWTF – Offensive Web Testing Framework
OWASP Offensive Web Testing Framework is a project focused on penetration testing efficiency and alignment of security tests to security standards like: The OWASP Testing Guide (v3 and v4), the OWASP Top 10, PTES and NIST. The purpose of this tool is to automate the manual and uncreative parts of pen testing. For example, Figuring […]