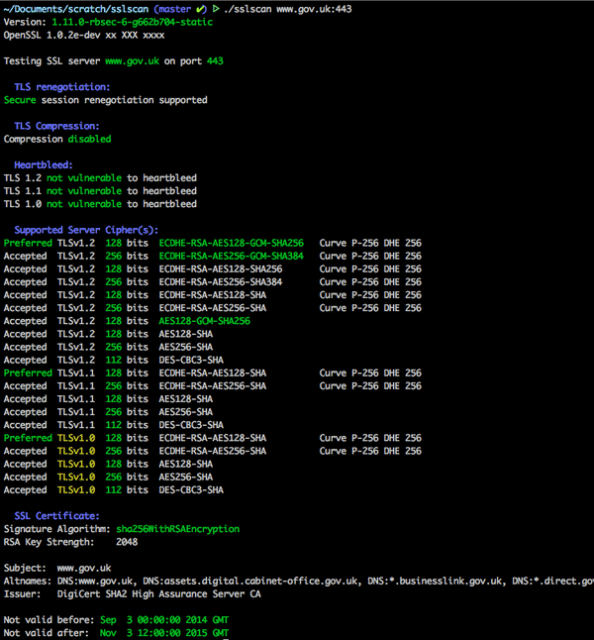
sslscan is a very efficient C program that allows you to detect SSL versions & cipher suites (including TLS version checker) and also checks for vulnerabilities like Heartbleed and POODLE.
A useful tool to keep around after you’ve set-up a server to check the SSL configuration is robust. Especially if you’re in an Internet limited environment and you can’t use an Online tool like the excellent Qualsys SSL Labs – https://www.ssllabs.com/ssltest/
sslscan Features – TLS Version Checker
sslscan has fairly complete support to detect all versions and ciphers for both SSL and TLS, including vulnerabilities (like Heartbleed and Poodle).
- Highlight SSLv2 and SSLv3 ciphers in output.
- Highlight CBC ciphers on SSLv3 (POODLE).
- Highlight 3DES and RC4 ciphers in output.
- Highlight PFS+GCM ciphers as good in output.
- Check for OpenSSL HeartBleed (CVE-2014-0160).
- Flag expired certificates.
- Flag weak DHE keys with OpenSSL >= 1.0.2.
- Experimental Windows & OS X support.
- Support for scanning PostgreSQL servers.
- StartTLS support for LDAP.
ssl scan Command Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 |
Command: [Options] [host:port | host] Options: --targets=<file> A file containing a list of hosts to check. Hosts can be supplied with ports (host:port) --sni-name=<name> Hostname for SNI --ipv4 Only use IPv4 --ipv6 Only use IPv6 --show-certificate Show full certificate information --no-check-certificate Don't warn about weak certificate algorithm or keys --show-client-cas Show trusted CAs for TLS client auth --show-ciphers Show supported client ciphers --show-cipher-ids Show cipher ids --show-times Show handhake times in milliseconds --ssl2 Only check SSLv2 ciphers --ssl3 Only check SSLv3 ciphers --tls10 Only check TLSv1.0 ciphers --tls11 Only check TLSv1.1 ciphers --tls12 Only check TLSv1.2 ciphers --tlsall Only check TLS ciphers (all versions) --ocsp Request OCSP response from server --pk=<file> A file containing the private key or a PKCS#12 file containing a private key/certificate pair --pkpass=<password> The password for the private key or PKCS#12 file --certs=<file> A file containing PEM/ASN1 formatted client certificates --no-ciphersuites Do not check for supported ciphersuites --no-fallback Do not check for TLS Fallback SCSV --no-renegotiation Do not check for TLS renegotiation --no-compression Do not check for TLS compression (CRIME) --no-heartbleed Do not check for OpenSSL Heartbleed (CVE-2014-0160) --starttls-ftp STARTTLS setup for FTP --starttls-imap STARTTLS setup for IMAP --starttls-irc STARTTLS setup for IRC --starttls-ldap STARTTLS setup for LDAP --starttls-pop3 STARTTLS setup for POP3 --starttls-smtp STARTTLS setup for SMTP --starttls-xmpp STARTTLS setup for XMPP --starttls-psql STARTTLS setup for PostgreSQL --xmpp-server Use a server-to-server XMPP handshake --http Test a HTTP connection --rdp Send RDP preamble before starting scan --bugs Enable SSL implementation bug work-arounds --timeout=<sec> Set socket timeout. Default is 3s --sleep=<msec> Pause between connection request. Default is disabled --xml=<file> Output results to an XML file <file> can be -, which means stdout --version Display the program version --verbose Display verbose output --no-cipher-details Disable EC curve names and EDH/RSA key lengths output --no-colour Disable coloured output --help Display the help text you are now reading |
You can download sslscan cipher detector here:
Or read more here.
