The ETOpen Ruleset is an excellent anti-malware IDS/IPS ruleset that enables users with cost constraints to significantly enhance their existing network-based malware detection. The ETOpen Ruleset is not a full coverage ruleset, and may not be sufficient for many regulated environments and should not be used as a standalone ruleset.
The ET Open ruleset is open to any user or organization, as long as you follow some basic guidelines. The ET Open ruleset is available for download any time without login.
Requirements
To use this ruleset you needs an IDS such as Snort or Suricata.
For much deeper information on what you should do, how to tune your ruleset and more check here:
You can’t and definitely shouldn’t try and run every rule.
Rule Categories
- Attack-Response Rules – These are designed to catch the results of a successful attack. Things like “id=root”, or error messages that indicate a compromise may have happened. Note: Trojan and virus post-infection activity is included generally in the VIRUS ruleset, not here.
- BotCC Rules – These are autogenerated from several sources of known and confirmed active Botnet and other Command and Control hosts. Updated daily, primary data source is Shadowserver.org.
- Compromised Rules – This is a list of known compromised hosts, confirmed and updated daily as well. This set varied from a hundred to several hunderd rules depending on the data sources. This is a compilation of several private but highly reliable data sources. Warming: Snort does not handle IP matches well load-wise. If your sensor is already pushed to the limits this set will add significant load. We recommend staying with just the BotCC rules in a high load case.
- Current_Events Rules – These are rules that we don’t intend to keep in the ruleset for long, or that need to be tested before they are considered for inclusion. Most often these will be simple sigs for the Storm binary URL of the day, sigs to catch CLSID’s of newly found vulnerable apps where we don’t have any detail on the exploit, etc. Useful sigs, but not for the long term.
- DOS Rules – Intended to catch inbound DOS activity, and outbound indications. Relatively self-explanatory.
- DROP Rules – This is a daily updated list of the Spamhaus DROP (Don’t Route or Peer) list. Primarily known professional spammers. More info at http://www.spamhaus.org
- DShield Rules – Daily updated list of the DShield top attackers list. Also very reliable. More indo at http://www.dshield.org
- Exploit Rules – Rules to detect direct exploits. Generally if you’re looking for a windows exploit, Veritas, etc, they’ll be here. Things like SQL injection and the like, whie they are exploits, have their own category.
- Game Rules – World of Warcraft, Starcraft, and other popular online games have sigs here. We don’t intend to label these things evil, just that they’re not appropriate for all environments.
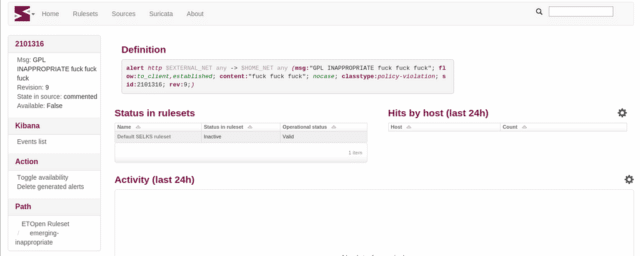
- Inappropriate Rules – Porn, Kiddy porn, sites you shouldn’t visit at work, etc. Warning: These are generally quite Regex heavy and thus high load and frequent false positives. Only run these if you’re really interested.
- Malware Rules – My personal favorite. This set was originally intended to be just spyware. That’s enough to several rule categories really. The line between spyware and outright malicious bad stuff has blurred to much since we originally started this set. There is more than just spyware in here, but rest assured nothing in here is something you want running on your net or PC. There are URL hooks for known update schemed, User-Agent strings of known malware, and a load of other goodies. If you can only run one ruleset to jsutify your IDS infrastructure, this is it!
- P2P Rules – Peer to Peer stuff. Bittorrent, Gnutella, Limewire, you name it. We’re not labeling these things Bad(tm), just not appropriate for all networks and environments.
- Policy Rules – Rules for things that are often disallowed by company or organizational policy. Myspace, Ebay, that kind of thing.
- RBN Rules – The Russian Business Network. These rules track the networks they’re known to own and regularly used. Updated whenever information changes.
- Scan Rules – Things to detect reconnaissance and probing. Nessus, Nikto, portscanning, etc. Early warning stuff.
- VOIP Rules – A new and emerging ruleset. Small at the moment, but we expect it to grow soon.
- Web Rules – Some SQL Injection, web server overflows, vulnerable web apps, that kind of thing. Very important if you’re running web servers, and pretty reasonable load.
- Web-SQL-Injection Rules – This is a large ruleset that intends to catch specific attacks on specific applications. There are some general SQL injection rules that work pretty well to catch most of what’s covered here. But these rules are much more specific to apps and web servers. Run this if you run a highly critical web farm, or are interested in having exact information about incoming web attacks.
The entire ruleset is available for download here:
https://rules.emergingthreats.net/
Or read more here.
