CapTipper is a Python tool to explore malicious HTTP traffic, it can also help analyse and revive captured sessions from PCAP files. It sets up a web server that acts exactly as the server in the PCAP file and contains internal tools with a powerful interactive console for analysis and inspection of the hosts, objects and conversations found.
The tool provides the security researcher with easy access to the files and the understanding of the network flow, and is useful when trying to research exploits, pre-conditions, versions, obfuscations, plugins and shell-codes.
Using CapTipper
Feeding CapTipper with a drive-by traffic capture (e.g of an exploit kit) displays the user with the requests URI’s that were sent and responses meta-data.
The user can at this point browse to http://127.0.0.1/[host]/[URI] and receive the response back to the browser. In addition, an interactive shell is launched for deeper investigation using various commands such as: hosts, hexdump, info, ungzip, body, client, dump and more.
|
1 |
Usage: ./CapTipper.py <PCAP_file> [-p] [web_server_port=80] |
Example
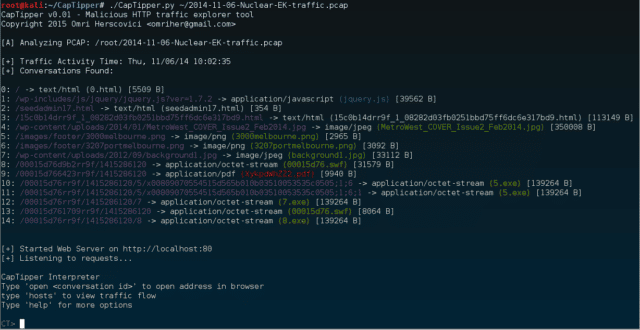
Analysing the following Nuclear EK drive-by infection PCAP: 2014-11-06-Nuclear-EK-traffic.pcap
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 |
C:\CapTipper> CapTipper.py "C:\NuclearFiles\2014-11-06-Nuclear-EK-traffic.pcap" CapTipper v0.1 - Malicious HTTP traffic explorer tool Copyright 2015 Omri Herscovici <omriher@gmail.com> [A] Analyzing PCAP: C:\NuclearFiles\2014-11-06-Nuclear-EK-traffic.pcap [+] Traffic Activity Time: Thu, 11/06/14 17:02:35 [+] Conversations Found: 0: / -> text/html (0.html) [5509 B] 1: /wp-includes/js/jquery/jquery.js?ver=1.7.2 -> application/javascript (jquery.js) [39562 B] 2: /seedadmin17.html -> text/html (seedadmin17.html) [354 B] 3: /15c0b14drr9f_1_08282d03fb0251bbd75ff6dc6e317bd9.html -> text/html (15c0b14drr9f_1_08282d03fb0251bbd75ff6dc6e317bd9.html) [113149 B] 4: /wp-content/uploads/2014/01/MetroWest_COVER_Issue2_Feb2014.jpg -> image/jpeg (MetroWest_COVER_Issue2_Feb2014.jpg) [350008 B] 5: /images/footer/3000melbourne.png -> image/png (3000melbourne.png) [2965 B] 6: /images/footer/3207portmelbourne.png -> image/png (3207portmelbourne.png) [3092 B] 7: /wp-content/uploads/2012/09/background1.jpg -> image/jpeg (background1.jpg) [33112 B] 8: /00015d76d9b2rr9f/1415286120 -> application/octet-stream (00015d76.swf) [31579 B] 9: /00015d766423rr9f/1415286120 -> application/pdf (XykpdWhZZ2.pdf) [9940 B] 10: /00015d76rr9f/1415286120/5/x00809070554515d565b010b03510053535c0505;1;6 -> application/octet-stream (5.exe) [139264 B] 11: /00015d76rr9f/1415286120/5/x00809070554515d565b010b03510053535c0505;1;6;1 -> application/octet-stream (5.exe) [139264 B] 12: /00015d76rr9f/1415286120/7 -> application/octet-stream (7.exe) [139264 B] 13: /00015d761709rr9f/1415286120 -> application/octet-stream (00015d76.swf) [8064 B] 14: /00015d76rr9f/1415286120/8 -> application/octet-stream (8.exe) [139264 B] [+] Started Web Server on http://localhost:80 [+] Listening to requests... CapTipper Interpreter Type 'open <conversation id>' to open address in browser type 'hosts' to view traffic flow Type 'help' for more options CT> |
You can download CapTipper here:
Or read more here.
