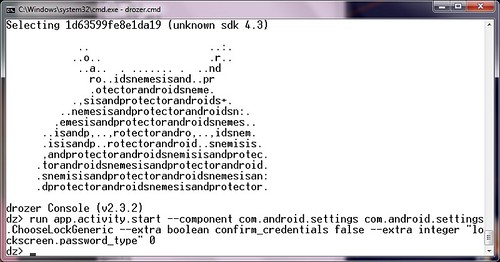
drozer (formerly Mercury) is the leading security testing framework for Android. drozer allows you to search for security vulnerabilities in apps and devices by assuming the role of an app and interacting with the Dalvik VM, other apps’ IPC endpoints and the underlying OS.
drozer provides tools to help you use, share and understand public Android exploits. It helps you to deploy a drozer Agent to a device through exploitation or social engineering. Using weasel (MWR’s advanced exploitation payload) drozer is able to maximise the permissions available to it by installing a full agent, injecting a limited agent into a running process, or connecting a reverse shell to act as a Remote Access Tool (RAT).
drozer helps to reduce the time taken for Android security assessments by automating the tedious and time-consuming. In a way you could think of drozer as Metasploit for Android devices.
- Discover and interact with the attack surface exposed by Android apps.
- Execute dynamic Java-code on a device, to avoid the need to compile and install small test scripts.
Features
- Discover Installed Packages
- Send Intents to IPC Endpoints
- Broadcast Intents
- Access Databases from other Apps
- Interact with Services in other Apps
- Arbitrary Java Execution
- Run an Interactive Shell
- Access a device with Remote Exploits
- Root Privilege Escalation
- Command-line Interface
- Use drozer with Physical Devices
- Use drozer with Android Emulators
You can download drozer here:
Windows installer – drozer-installer-2.3.3.zip
Debian/Ubuntu (.deb) – drozer_2.3.3.deb
Redhat/CentOS (.rpm) – drozer-2.3.3-1.noarch.rpm
Or read more here.
