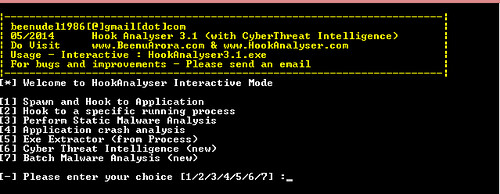
Hook Analyser is a freeware application which allows an investigator/analyst to perform “static & run-time / dynamic” analysis of suspicious applications, also gather (analyse & co-related) threat intelligence related information (or data) from various open sources on the Internet.
Essentially it’s a malware analysis tool that has evolved to add some cyber threat intelligence features & mapping.
Hook Analyser is perhaps the only “free” software in the market which combines analysis of malware analysis and cyber threat intelligence capabilities. The software has been used by major Fortune 500 organisations.
Features/Functionality
- Spawn and Hook to Application – Enables you to spawn an application, and hook into it
- Hook to a specific running process – Allows you to hook to a running (active) process
- Static Malware Analysis – Scans PE/Windows executables to identify potential malware traces
- Application crash analysis – Allows you to analyse memory content when an application crashes
- Exe extractor – This module essentially extracts executables from running process/s
The only similar tool I recall is – Malware Analyser v3.0 – A Static & Dynamic Malware Analysis Tool – which is by the same author and I assume is the precursor the more advanced Hook Analyser.
You can download Hook Analyser v3.1 here:
[ Required to fill out a form ]
Or read more here.
