This Hackers Manifesto is a seminal piece of writing from the underground, the ultimate hacker text, forgotten by many but adored by many more. It still resonates with me and has as much meaning as it did back in the day when I first read it in Phrack Issue 7.
If you don’t know anything about the Hacker Manifesto or have never even heard of it, read it and read it carefully. It dates back to 1986 and was penned by Loyd Blankenship AKA The Mentor shortly after his arrest by the FBI for computer related crimes (more at Wikipedia).
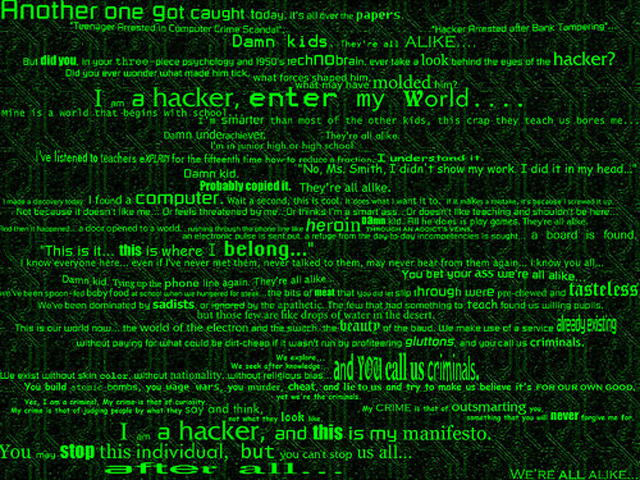
The Hackers Manifesto – Hacker Text
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 |
Another one got caught today, it's all over the papers. "Teenager Arrested in Computer Crime Scandal", "Hacker Arrested after Bank Tampering"... Damn kids. They're all alike. But did you, in your three-piece psychology and 1950's technobrain, ever take a look behind the eyes of the hacker? Did you ever wonder what made him tick, what forces shaped him, what may have molded him? I am a hacker, enter my world... Mine is a world that begins with school... I'm smarter than most of the other kids, this crap they teach us bores me... Damn underachiever. They're all alike. I'm in junior high or high school. I've listened to teachers explain for the fifteenth time how to reduce a fraction. I understand it. "No, Ms. Smith, I didn't show my work. I did it in my head..." Damn kid. Probably copied it. They're all alike. I made a discovery today. I found a computer. Wait a second, this is cool. It does what I want it to. If it makes a mistake, it's because I screwed it up. Not because it doesn't like me... Or feels threatened by me... Or thinks I'm a smart ass... Or doesn't like teaching and shouldn't be here... Damn kid. All he does is play games. They're all alike. And then it happened... a door opened to a world... rushing through the phone line like heroin through an addict's veins, an electronic pulse is sent out, a refuge from the day-to-day incompetencies is sought... a board is found. "This is it... this is where I belong..." I know everyone here... even if I've never met them, never talked to them, may never hear from them again... I know you all... Damn kid. Tying up the phone line again. They're all alike... You bet your ass we're all alike... we've been spoon-fed baby food at school when we hungered for steak... the bits of meat that you did let slip through were pre-chewed and tasteless. We've been dominated by sadists, or ignored by the apathetic. The few that had something to teach found us will- ing pupils, but those few are like drops of water in the desert. This is our world now... the world of the electron and the switch, the beauty of the baud. We make use of a service already existing without paying for what could be dirt-cheap if it wasn't run by profiteering gluttons, and you call us criminals. We explore... and you call us criminals. We seek after knowledge... and you call us criminals. We exist without skin color, without nationality, without religious bias... and you call us criminals. You build atomic bombs, you wage wars, you murder, cheat, and lie to us and try to make us believe it's for our own good, yet we're the criminals. Yes, I am a criminal. My crime is that of curiosity. My crime is that of judging people by what they say and think, not what they look like. My crime is that of outsmarting you, something that you will never forgive me for. I am a hacker, and this is my manifesto. You may stop this individual, but you can't stop us all... after all, we're all alike. +++The Mentor+++ |
I found an ancient copy of The Hackers Manifesto when I was switching over the new server and thought it’d probably be better if I posted it up here on the new site instead of in the nasty old HTML.
I guess many of you have read it before, and I hope you enjoy reading it again. My main aim though is to introduce it to newer people in the industry and hope they share it amongst their peers as it still embodies the hacker ethos and is the ultimate hacker manifesto.
If you enjoyed this you can also check out the seminal hacking piece Writing Worms for Fun or Profit.

GZero says
I read this when I was about 9. Really never looked back.
Thanks.
und3r says
This testimony was rediscovered, The Mentor, got up for an ethics indescribable, The Mentor, forever in our memories!
Embraces, MEL !
TheLightcosine says
wow, now that brings back some memories!
Navin says
On the same page as GZero….read it when I was very young!
This and Mitnick’s The Art Of Deception are arguably the most influential pieces of literature I’ve read! :)
Rishabh Dangwal says
Ditto here..read it when I was 11..read one of books by the now script kiddie Ankit fadiya back then and was hooked to zines when grew a bit older.. The manifesto always motivatesd me to do a bit more..
CBRP1R8 says
Read it a few years after it came out, but I do remember the story as well, no truer words spoken. Was part of the Free Kevin Campaign…
:D
Calico Jack says
In a similar vein.
Articles of Internet Piracy.
Article 1:
A Pirate has no dealings with criminals, be they suits or gangstas.
Copying is not stealing for nothing is taken. We seek to own only that which has been made falsely scarce. A Pirate takes not the just profit from those that create content, instead we deny it to those middlemen that steal from all and contribute nothing. For we are not lost sales if we could never buy it anyway. We support not the broken business models of greedy industries.
Article 2:
Any Pirate has equal title to those fresh warez, or strongly seeded torrents as may be found, and use of them at Pleasure. For preferance d/l only clean legal content, unless a Scarcity make it necessary to obtain them otherwise.
Article 3:
Every Pirate must obey civil usage:
For every torrent downloaded, seed at least 1:2 ratio.
Unless your bandwidth be meager, then seed after you’ve d/l’ed by 1:1.
A pirate is not a leech.
Article 4:
Only d/l what content you can’t afford to see or hear otherwise.
Support the artists as much as you can. If you cannot pay them, do not keep them a secret but spread the word and encourage others to buy their work. Reputation and word of mouth be free, and priceless.
Article 5:
Any person who poisons a torrent, or finds and does not report a poisoned torrent, deserves to be shunned, banned or mocked without mercy, until their rep be deep sixed.
Article 6:
Any Pirate, that betrays another pirate to the authorities or his ISP, shall suffer whatever punishment as /b/stards deem fit to dish out.
under01 says
I believe more of the old hackers we have first the Cyberpunk Code.
DL says
thx for good memories!
V says
well that was interesting.
pieface says
This also features in the 2600 hackers odyssey year book,only read the article recently,intresting piece.
Pronoein says
Where and how can I contact an authentic community of hackers with such an code?