Sguil (pronounced sgweel) is probably best described as an aggregation system for network security monitoring tools. It ties your IDS alerts into a database of TCP/IP sessions, full content packet logs and other information. When you’ve identified an alert that needs more investigation, the sguil client provides you with seamless access to the data you need to decide how to handle the situation. In other words, sguil simply ties together the outputs of various security monitoring tools into a single interface, providing you with the most information in the shortest amount of time.
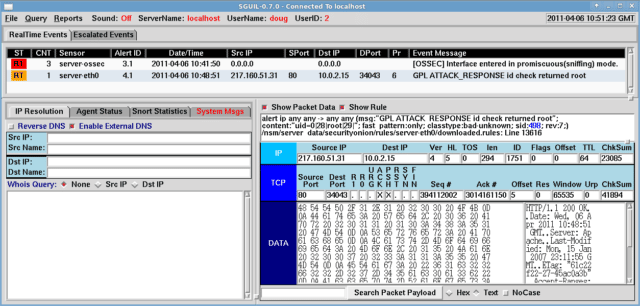
Sguil uses a database backend for most of its data, which allows you to perform SQL queries against several different types of security events.
How is sguil different from Snort + ACID or Snort + BASE?
ACID & BASE are both web-based IDS alert management systems. They let you browse and search alerts, but don’t offer very much in the way of data-mining that would allow you to answer questions like, “Was this an attack attempt or a false positive?”, “Was the attempt successful?” or “What other machines did the attacker try to crack once he got into this one?”. They rely on you to do the research necessary to determine the severity of the situation.
Sguil’s design centers on providing convenient, quick access to a host of supporting information, which both saves you time and helps you make better decisions. Incidentally, because sguil uses a dedicated client instead of running through a web browser, you get a richer, more responsive user interface as well.
You can find snort here:
You can read more and download Sguil here:

mubix says
The people from SQUIL gave a talk at ShmooCon 06 and I was quite impressed with it then, but I never had the time to dedicate to get it working. Dark, have you gotten it working and, if so, do you like it? Does it have Snort configuration options? Can I tell it to ignore the very annoying “DOUBLE DECODING ATTACK” alert?
Hanashi says
mubix, NSMWiki, the official Sguil wiki, has a section for Installation and HOWTO guides. You’ll find some pretty detailed instructions, which should take some of the pain out of it. If you’re on RHEL, you can even use InstantNSM to automate most of the install.
And yes, you can configure sguil to ignore alerts like that, but it’s probably better to tune Snort itself so that they are never generated in the first place.
BTW, most of the text in this article was cribbed from the Sguil FAQ. Thanks to the Darknet folks for promoting sguil, just please remember to cite your source next time.
Darknet says
mubix: I’d echo what Hanashi said, you are better off configuring your sensors properly so they don’t generate the alert rather than filtering it out in the results. It’s pretty easy to setup and I do like it, I tend to use the web-based systems more though as I find them more portable (I can access from anywhere).
Hanashi: Will add the source link in when your FAQ is back up. I don’t tend to link source for tool/software posts at it can be assumed the text is from the site being linked to. Cheers!
Torvaun says
Ooh, new toy to play with, on company time no less. Will review and report back later.