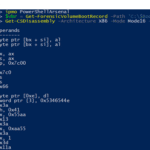
PowerShellArsenal is basically PowerShell for reverse engineering in a module format. The module can be used to disassemble managed and unmanaged code, perform .NET malware analysis, analyse/scrape memory, parse file formats and memory structures, obtain internal system information, etc. PowerShellArsenal is comprised of the following tools: Disassembly – Disassemble native and managed code. MalwareAnalysis – […]
windows forensics
FastIR Collector – Windows Incident Response Tool
FastIR Collector is Windows incident response tool that offers the possibility to extract classic artefacts such as memory dump, auto-started software, MFT, MBR, Scheduled tasks, Services and records the results in csv files. The tool can also perform smart acquisitions thanks to the filecatcher, certificate filtering or support of Yara rules. The first part of […]
Rekall – Memory Forensic Framework
Rekall is a memory forensic framework that provides an end-to-end solution to incident responders and forensic analysts. From state of the art acquisition tools, to the most advanced open source memory analysis framework. It strives to be a complete end-to-end memory forensic framework, encapsulating acquisition, analysis, and reporting. In particular Rekall is the only memory […]
StreamArmor – Discover & Remove Alternate Data Streams (ADS)
[ad] StreamArmor is a tool for discovering hidden alternate data streams (ADS) and can also clean them completely from the system. It’s advanced auto analysis coupled with online threat verification mechanism makes it the best tool available in the market for eradicating the evil streams. StreamArmor comes with fast multi threaded ADS scanner which can […]
Want Some COFEE? Microsoft Computer Online Forensic Evidence Extractor
[ad] Microsoft helping the good guys eh? I had someone ask me if I can get a hold of this so I did some checking up on.. I’d guess MS is doing this to sell additional software and services, but either way its a good thing to make a portable, easy to use and effective […]