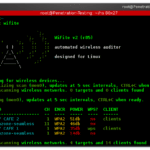
wifite is created to attack multiple WEP and WPA encrypted networks at the same time. This tool is customizable to be automated with only a few arguments and can be trusted to run without supervision. It’s a great tool to script into part of a toolkit for Wifi security assessments and is a handy wifi […]
wep-cracking
WEPBuster – Wireless Security Assessment Tool – WEP Cracking
[ad] WEPBuster basically seems to be a toolkit that attempts to automate the tasks done by the various parts of the aircrack-ng suite. The end goal of course is to crack the WEP key of a given Wireless network. Features The main part of this is the autonomous nature of the toolkit, it can crack […]
Russix – LiveCD Linux Distro for Wireless Penetration Testing & WEP Cracking
It looks like it might be time to update our very well received list of the 10 Best Security Live CD Distros (Pen-Test, Forensics & Recovery) since we have Russix now and Backtrack new version is on the way out. Russix is a Slax based Wireless Live Linux. It has been designed to be light […]
KisMAC – Free WiFi Stumbler/Scanner for Mac OS X
KisMAC is an opensource and free stumbler/scanner application for Mac OS X. It has an advantage over MacStumbler/iStumbler/NetStumbler in that it uses monitor mode and passive scanning. KisMAC supports several third party PCMCIA cards – Orinoco, PrismII, Cisco Aironet, Atheros and PrismGT. USB Prism2 is supported as well, and USB Ralink support is in development. […]
aircrack-ng – WEP and WPA-PSK Key Cracking Program
aircrack is an 802.11 WEP and WPA-PSK keys cracking program that can recover keys once enough data packets have been captured. It implements the standard FMS attack along with some optimizations like KoreK attacks, thus making the attack much faster compared to other WEP cracking tools. In fact, aircrack is a set of tools for […]