Infernal Twin is an automated wireless hacking suite written in Python which automates many of the repetitive tasks involved in security testing for wifi networks. Originally created to automate the Evil Twin attack, it has grown much beyond that into a comprehensive suite including various wireless attack vectors. An evil twin attack is when a […]
evil twin attack
Linset Download – Evil Twin Attack Hacking Tool
Linset is an Evil Twin Attack Hacking Tool with everything built in (multi-lingual web page, DHCP, DNS server with redirect fake AP etc) so it has a bunch of dependencies, and it’s in Spanish. But other than that, it’s pretty cool. It’s also a recursive acronym – Linset Is Not a Social Enginering Tool. There […]
Infernal Twin – Automatic Wifi Hacking Tool
Infernal Twin is an automatic wifi hacking tool, basically a Python suite created to aid penetration testers during wireless assessments, it automates many of the common attacks – which can get complicated and hard to manage when executed manually. The author noticed a gap in the market with there being many tools to automate web […]
EvilAP Defender – Detect Evil Twin Attacks
EvilAP_Defender is an application that helps wireless network administrators to discover and prevent Evil Access Points (AP) from attacking wireless users. The application can be run in regular intervals to protect your wireless network and detect Evil Twin attacks. By configuring the tool you can get notifications sent to your email whenever an evil access […]
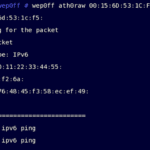
Wep0ff – Wireless WEP Key Cracker Tool
Wep0ff is new WEP Key Cracker that can function without access to AP, it works by mounting a fake access point attack against WEP-based wireless clients. It uses a combination of fragmentation and evil twin attacks to generate traffic which can be used for KoreK-style WEP-key recovery. This tool can be used to mount fake […]