PenTools is a bundle of Python and Bash penetration testing tools for the recon and information gathering stage of a PT or VA. They are fairly simple scripts but might be interesting if you are new and want to see how some things are done, or how things can be automated using Python or Bash. […]
bash
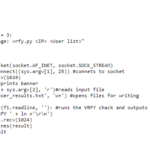
unix-privesc-check – Unix/Linux User Privilege Escalation Scanner
Unix-privesc-checker is a Unix/Linux User privilege escalation scanner that runs on Unix systems (tested on Solaris 9, HPUX 11, Various Linuxes, FreeBSD 6.2). It tries to find misconfigurations that could allow local unprivileged users to escalate privileges to other users or to access local apps (e.g. databases). It’s similar in some ways to – LinEnum […]
Graudit v1.9 Download – Grep Source Code Auditing Tool
Graudit is a simple script and signature sets that allows you to find potential security flaws in source code using the GNU utility grep. It’s comparable to other static analysis applications and source code auditing tool sets like RATS, SWAAT and flaw-finder while keeping the technical requirements to a minimum and being very flexible. You […]
Everything You NEED To Know About Shellshock Bug In BASH
Shellshock (CVE-2014-6271) the bug in BASH is causing havoc on the Internet this week, as far as I’m concerned it’s a bit overstated – seriously how many people are still using cgi scripts? None I hope. I do suspect though a lot of shared hosts might get owned by this as most commercial control panel […]
Shelling our way up
[ad] Everybody has a favorite shell; not so many under Windows as there are under Linux, but anyway… As most will tell you there favorite shell under Linux would be bash, as under Windows not really having what to chose from they would say cmd.exe (ok, bash can be used under Windows via cygwin, if […]