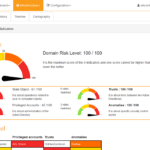
PingCastle is a Active Directory Security Assessment Tool designed to quickly assess the Active Directory security level with a methodology based on a risk assessment and maturity framework. It does not aim at a perfect evaluation but rather as an efficiency compromise. The risk level regarding Active Directory security has changed. Several vulnerabilities have been […]
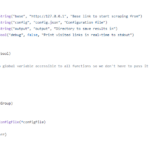
Second Order – Subdomain Takeover Scanner Tool
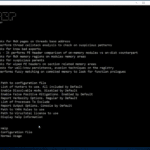
Second Order Subdomain Takeover Scanner Tool scans web applications for second-order subdomain takeover by crawling the application and collecting URLs (and other data) that match specific rules or respond in a specific way. Using Second Order Subdomain Takeover Scanner Tool Command line options:
|
1 2 3 4 5 6 7 8 |
-base string Base link to start scraping from (default "http://127.0.0.1") -config string Configuration file (default "config.json") -debug Print visited links in real-time to stdout -output string Directory to save results in (default "output") |
Example:
|
1 |
go run second-order.go -base https://example.com -config config.json -output example.com -concurrency 10 |
Config File for Second Order Subdomain Takeover Scanner Tool […]
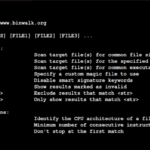
Binwalk – Firmware Security Analysis & Extraction Tool
Binwalk is a fast and easy to use Python-based firmware security analysis tool that allows for firmware analysis, reverse engineering, and extraction of firmware images. Features of Binwalk Firmware Security Analysis & Extraction Tool Scanning Firmware – Binwalk can scan a firmware image for many different embedded file types and file systems File Extraction – […]
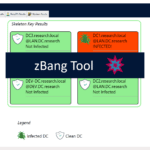
zBang – Privileged Account Threat Detection Tool
zBang is a risk assessment tool for Privileged Account Threat Detection on a scanned network, organizations and red teamers can utilize zBang to identify potential attack vectors and improve the security posture of the network. The results can be analyzed with the graphic interface or by reviewing the raw output files. The tool is built […]
Memhunter – Automated Memory Resident Malware Detection
Memhunter is an Automated Memory Resident Malware Detection tool for the hunting of memory resident malware at scale, improving the threat hunter analysis process and remediation times. It’s a self contained binary that can be deployed and managed at scale, does not use memory dumps and relies purely on memory inspection to do its work. […]