So there’s been a fair bit of noise this past week about the Mac OS X Ransomware, the first of its’ kind called KeRanger. It also happens to be the first popular Mac malware of any form for some time. It’s also a lesson to all the Apple fanbois that their OS is not impervious […]
Malware
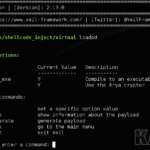
Veil Framework – Antivirus Evasion Framework
The Veil-Framework is a collection of red team security tools that implement various attack methods focused on antivirus evasion and evading detection. Antivirus ‘solutions’ don’t often catch the bad guys, but they do often catch pen-testing during assignment. This tool came about as a way to execute existing shellcode in a way that could evade […]
YARA – Pattern Matching Tool For Malware Analysis
YARA is a tool aimed at (but not limited to) helping malware researchers to identify and classify malware samples. With YARA you can create descriptions of malware families (or whatever you want to describe) based on textual or binary patterns. Each description, a.k.a rule, consists of a set of strings and a boolean expression which […]
DAMM – Differential Analysis of Malware in Memory
Differential Analysis of Malware in Memory (DAMM) is a tool built on top of Volatility Framework. Its main objective is as a test bed for some newer techniques in memory analysis, including performance enhancements via persistent SQLite storage of plugin results (optional); comparing in-memory objects across multiple memory samples, for example processes running in an […]
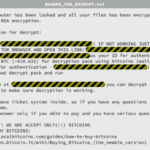
FBI Recommends Crypto Ransomware Victims Just Pay
Crypto ransomware is a type of malware that holds you ransom by encrypting your files and has been around for a while, but the FBI recently said at a cyber security summit that they advise companies that fall victim just to pay. Such malware tends to use pretty strong encryption algorithms like RSA-2048, which you […]