Whilst I was away on a tropical island enjoying myself the Infosec Internet was on fire with news of the global WannaCry ransomware threat which showed up in the UK NHS and was spreading across 74 different countries. The Ransomware seems to be the first that is P2P using an SMB exploit from the NSA […]
Malware
Hajime Botnet Reaches 300,000 Hosts With No Malicious Functions
This is not the first IoT heavy botnet, Mirai takes that title, the interesting part is the Hajime botnet appears to be benign. So far no malicious functions have been detected in the codebase, other than the ability to replicate itself and block other malware, Hajime seems to have no DDoS or offensive mechanisms. Hajime […]
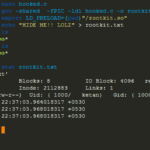
BEURK – Linux Userland Preload Rootkit
BEURK is an userland preload rootkit for GNU/Linux, heavily focused around anti-debugging and anti-detection. Being a userland rootkit it gives limited privileges (whatever the user has basically) vs a superuser or root level rootkit. Features Hide attacker files and directories Realtime log cleanup (on utmp/wtmp) Anti process and login detection Bypass unhide, lsof, ps, ldd, […]
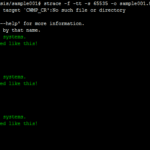
yarAnalyzer – Yara Rule Analyzer and Statistics Generator
yarAnalyzer is a Python-based YARA rule analyzer that can also generate statistics from yara rulesets. It also has an inventory creation feature that can output a CSV file detailing the rules. It creates statistics on a YARA rule set and files in a sample directory. Place some signatures with .yar extension in the “signatures” folder […]
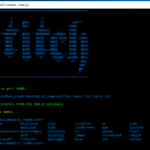
Stitch – Python Remote Administration Tool AKA RAT
Stitch is a cross-platform Python Remote Administration Tool, commonly known as a RAT. This framework allows you to build custom payloads for Windows, Mac OSX and Linux as well. You are able to select whether the payload binds to a specific IP and port, listens for a connection on a port, option to send an […]