Whilst I was away on a tropical island enjoying myself the Infosec Internet was on fire with news of the global WannaCry ransomware threat which showed up in the UK NHS and was spreading across 74 different countries. The Ransomware seems to be the first that is P2P using an SMB exploit from the NSA […]
Exploits/Vulnerabilities
Intel Finally Patches Critical AMT Bug (Kinda)
Intel finally patches the critical AMT bug discovered in March by security researcher Maksim Malyutin at Embedi, I say ‘kinda’ because it’s not really up to Intel to deploy the fix to the problem. They can’t really push out updates to CPUs, but at least they have fixed it in the firmware and now the […]
Shadow Brokers Release Dangerous NSA Hacking Tools
It’s not the first time Shadow Brokers has been on the radar with NSA Hacking Tools, in August 2016 they exposed a bunch of 0-day exploits (also from 2013). This cache of tools appears to be from 2013, so was probably snatched during the same intrusion. This is somewhat more dangerous though as it provides […]
PowerMemory – Exploit Windows Credentials In Memory
PowerMemory is a PowerShell based tool to exploit Windows credentials present in files and memory, it levers Microsoft signed binaries to hack Windows. The method is totally new. It proves that it can be extremely easy to get credentials or any other information from Windows memory without needing to code in C-type languages. In addition, […]
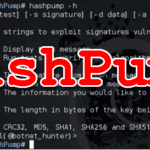
HashPump – Exploit Hash Length Extension Attack
HashPump is a C++ based command line tool to exploit the Hash Length Extension Attack with various hash types supported, including MD4, MD5, SHA1, SHA256, and SHA512. There’s a good write-up of how to use this in practical terms here: Plaid CTF 2014: mtpox Usage
|
1 2 3 4 5 6 7 8 9 10 11 |
$ hashpump -h HashPump [-h help] [-t test] [-s signature] [-d data] [-a additional] [-k keylength] HashPump generates strings to exploit signatures vulnerable to the Hash Length Extension Attack. -h --help Display this message. -t --test Run tests to verify each algorithm is operating properly. -s --signature The signature from known message. -d --data The data from the known message. -a --additional The information you would like to add to the known message. -k --keylength The length in bytes of the key being used to sign the original message with. Version 1.2.0 with CRC32, MD5, SHA1, SHA256 and SHA512 support. <Developed by bwall(@botnet_hunter)> |
You can download HashPump here:
|
1 2 3 4 5 |
$ git clone https://github.com/bwall/HashPump.git $ apt-get install g++ libssl-dev $ cd HashPump $ make $ make install |
Or read more […]