zANTI is an Android Wireless Hacking Tool that functions as a mobile penetration testing toolkit that lets you assess the risk level of a network using your mobile device for free download. This easy to use mobile toolkit enables IT Security Administrators to simulate an advanced attacker to identify the malicious techniques they use in […]
Search Results for: android
dSploit APK Download – Hacking & Security Toolkit For Android
dSploit APK Download is a Hacking & Security Toolkit For Android which can conduct network analysis and penetration testing activities. It aims to offer to IT security experts the most complete and advanced professional toolkit to perform network security assessments on a mobile device. Once dSploit is started, you will be able to easily map […]
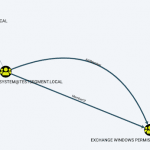
Intercepter-NG – Android App For Hacking
Intercepter-NG is a multi functional network toolkit including an Android app for hacking, the main purpose is to recover interesting data from the network stream and perform different kinds of MiTM attacks. Specifically referring to Intercepter-NG Console Edition which works on a range of systems including NT, Linux, BSD, MacOSX, IOS and Android. The Windows […]
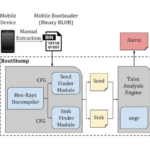
BootStomp – Find Android Bootloader Vulnerabilities
BootStomp is a Python-based tool, with Docker support that helps you find two different classes of Android bootloader vulnerabilities and bugs. It looks for memory corruption and state storage vulnerabilities. Note that BootStomp works with boot-loaders compiled for ARM architectures (32 and 64 bits both) and that results might slightly vary depending on angr and […]
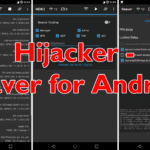
Hijacker – Reaver For Android Wifi Hacker App
Hijacker is a native GUI which provides Reaver for Android along with Aircrack-ng, Airodump-ng and MDK3 making it a powerful Wifi hacker app. It offers a simple and easy UI to use these tools without typing commands in a console and copy & pasting MAC addresses. Features of Hijacker Reaver For Android Wifi Hacker App […]