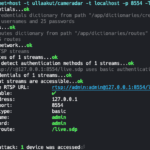
Cameradar is a Go-based tool to hack RTSP Video Surveillance CCTV Cameras, it can detect open RTSP hosts, detect device models and launch automated attacks. The main features of Cameradar are: Detect open RTSP hosts on any accessible target host Detect which device model is streaming Launch automated dictionary attacks to get their stream route […]
Archives for January 2020
dSploit APK Download – Hacking & Security Toolkit For Android
dSploit APK Download is a Hacking & Security Toolkit For Android which can conduct network analysis and penetration testing activities. It aims to offer to IT security experts the most complete and advanced professional toolkit to perform network security assessments on a mobile device. Once dSploit is started, you will be able to easily map […]
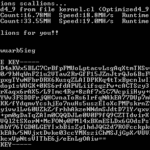
Scallion – GPU Based Onion Hash Generator
Scallion is a GPU-driven Onion Hash Generator written in C#, it lets you create vanity GPG keys and .onion addresses (for Tor’s hidden services) using OpenCL. Scallion runs on Mono (tested in Arch Linux) and .NET 3.5+ (tested on Windows 7 and Server 2008) Scallion was used to find collisions for every 32bit key id […]