Sooty is a tool developed with the task of aiding a SOC analyst to automate parts of their workflow and speed up their process.
The main goal of Sooty is to perform as much of the routine checks as possible which allows the analyst more time to spend on deeper analysis.
Features of Sooty SOC Analyst CLI Tool
- Sanitise URL’s to be safe to send in emails
- Perform reverse DNS and DNS lookups
- Perform reputation checks from:
- Check if an IP address is a TOR exit node
- Decode Proofpoint URL’s, UTF-8 encoded URLS, Office SafeLink URL’s and Base64 Strings
- Get file hashes and compare them against VirusTotal (see requirements)
- Perform WhoIs Lookups
- Check Usernames and Emails against HaveIBeenPwned to see if a breach has occurred. (see requirements)
- Simple analysis of emails to retrieve URL’s, emails and header information.
- Extract IP addresses from emails.
- Unshorten URL’s that have been shortened by external services. (Limited to 10 requests per hour)
- Query URLScan.io for reputation reports.
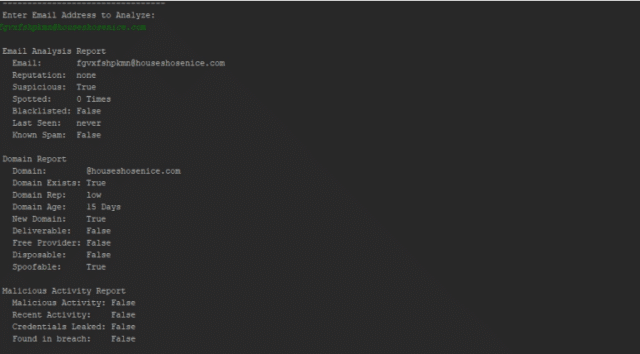
- Analyze email addresses for known malicious activity and report on domain reputation utilising EmailRep.io
- Create dynamic email templates that can be used as a base for phishing triage response.(.msg only, .eml coming in future update)
Installing Sooty SOC Analyst CLI Tool
- Python 3.x
- Install all dependencies from the requirements.txt file.
pip install -r requirements.txt - To use the Hash comparison with VirusTotal requires an API key, replace the key
VT_API_KEYin the code with your own key. The tool will still function without this key, however this feature will not work. - To use the Reputation Checker with AbuseIPDB requires an API Key, replace the key
AB_API_KEYin the code with your own key. The tool will still function without this key, however this feature will not work. - To use the URLScan.io checker function with URLScan requires an API Key, replace the key
URLSCAN_IO_KEYin the code with your own key. The tool will still function without this key, however this feature will not work. - Use of the HaveIBeenPwned functionality requires an API Key, replace the key
HIBP_API_KEYin the code with your own key. The tool will still function without this key, however this feature will not work.
You can download Sooty here:
Or read more here.
