NetBScanner is a NetBIOS network scanner tool that scans all computers in the IP addresses range you choose, using the NetBIOS protocol.
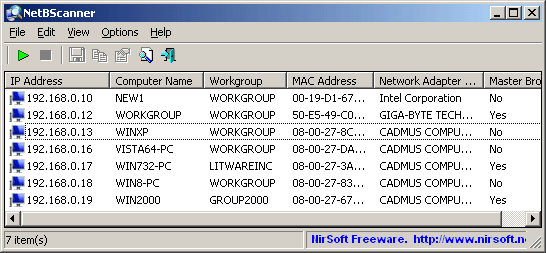
For every computer located by this NetBIOS scanner, the following information is displayed:
- IP Address
- Computer Name
- Workgroup or Domain
- MAC Address
- Network adapter manufacturer (from MAC address).
NetBScanner also shows whether a computer is a Master Browser. You can easily select one or more computers found by NetBScanner, and then export the list into csv/tab-delimited/xml/html file.
NetBIOS Network Scanner System Requirements
- This utility works on every version of Windows, starting from Windows 2000 and up to Windows 10, including both 32-bit systems and x64 systems.
- NetBIOS scan uses UDP port 137 to send and receive the NetBIOS data. If this port is blocked by your computer or in the remote network computers that you scan, the NetBIOS scan will not work.
- When you run NetBScanner in the first time, you might get a warning from the Firewall of Windows. Even if you choose to keep blocking NetBScanner, the NetBIOS scan will still work properly.
Using NetBScanner NetBIOS Scanner
NetBScanner doesn’t require any installation process or additional dll files. In order to start using it, simply run the executable file – NetBScanner.exe
After running NetBScanner, you have to choose the IP addresses range to scan (by default, NetBScanner takes the IP addresses range from the configuration of your network adapter) and the scan speed. Be aware that if you increase the scan speed, the NetBIOS scan may become less reliable and miss some of your computers.
After you choose the desired scan option, click the ‘Ok’ button, and then NetBScanner will start scanning your network.
After the NetBIOS scan is finished, you can select one or more computers, and then export the computers list into csv/tab-delimited/xml/html file, by using the ‘Save Selected Items’ option (Ctrl+S)
Command-line Options for NetBIOS Scanning
|
1 2 3 4 5 6 |
/scan Start to scan immediately on start. /IPAddressFrom <IP Address> /IPAddressTo <IP Address> Specifies the IP addresses range to scan, for example: NetBScanner.exe /scan /IPAddressFrom 192.168.1.0 /IPAddressTo 192.168.1.254 /ScanSpeed <Speed> Specifies the scanning speed. The speed is a number between 0 and 100. 0 = very slow, 100 = very fast |
Also check out:
– nbtscan Download – NetBIOS Scanner For Windows & Linux
You can download NetBScanner here:
Or read more here.
