Enumall is a Python-based tool that helps you do subdomain discovery using only one command by combining the abilities of Recon-ng and AltDNS. This gives you the ability to run multiple domains within the same session. The tool only has one module that needs an API key (/api/google_site) find instructions for that on the recon-ng […]
Archives for July 2018
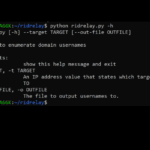
RidRelay – SMB Relay Attack For Username Enumeration
RidRelay is a Python-based tool to enumerate usernames on a domain where you have no credentials by using a SMB Relay Attack with low privileges. How RidRelay SMB Relay Attack Works RidRelay combines the SMB Relay attack, common lsarpc based queries and RID cycling to get a list of domain usernames. It takes these steps: […]
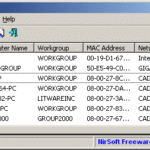
NetBScanner – NetBIOS Network Scanner
NetBScanner is a NetBIOS network scanner tool that scans all computers in the IP addresses range you choose, using the NetBIOS protocol. For every computer located by this NetBIOS scanner, the following information is displayed: IP Address Computer Name Workgroup or Domain MAC Address Network adapter manufacturer (from MAC address). NetBScanner also shows whether a […]