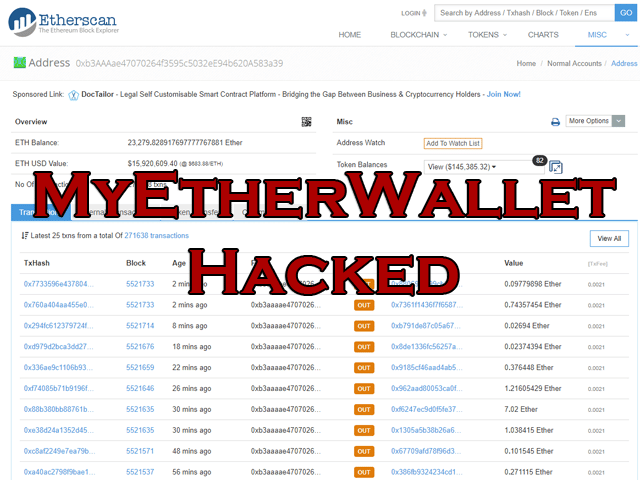
Big news in the crypto scene this week was that the MyEtherWallet DNS Hack that occured managed to collect about $17 Million USD worth of Ethereum in just a few hours.
The hack itself could have been MUCH bigger as it actually involved compromising 1300 Amazon AWS Route 53 DNS IP addresses, fortunately though only MEW was targetted resulting in the damage being contained in the cryptosphere (as far as we know anyway).
Crooks today hijacked internet connections to Amazon Web Services systems to ultimately steal a chunk of alt-coins from online cryptocurrency website MyEtherWallet.com.
The Ethereum wallet developer confirmed on Tuesday morning that thieves redirected DNS lookups for its dot-com to a malicious website masquerading as the real thing. That meant some people logging in to MyEtherWallet.com were really connecting to a bogus site and handing over their details to criminals, who promptly drained ETH from their marks’ wallets.
Victims had to click through a HTTPS error message, as the fake MyEtherWallet.com was using an untrusted TLS/SSL certificate. The bandits have amassed $17m in Ethereum in their own wallet over time.
Crucially, this DNS hijacking was possible after miscreants pulled off a classic BGP hijacking attack on AWS. MyEtherWallet.com uses Amazon’s Route 53 DNS service so that when people try to visit the dot-com, AWS looks up and returns to web browsers the IP addresses of the wallet website’s web servers.
Between 11am and 1pm UTC today, someone was able to send BGP – Border Gateway Protocol – messages to the internet’s core routers to convince them to send traffic destined for some of AWS’s servers to a renegade box in the US.
That rogue machine then acted as AWS’s DNS service, and gave out the wrong IP addresses for MyEtherWallet.com, pointing some unlucky visitors to the dot-com at a phishing site that stole their money.
It’s a shame people aren’t more careful as the SSL certificate wouldn’t match, so there was a browser warning for everyone that visited. I saw one guy that lost 85 ETH, which is a fairly significant amount for anyone.
As far as attacks go it’s a fairly sophisticated one targetting DNS and using BGP hijacking to route the traffic to an owned box in the US.
Of course BGP takes and DNS Hijacks are nothing new and have been going on for years like the mass domain hijacking via the Gandi.net DNS hack.
“As soon as I logged in [to myetherwallet.com], there was a countdown for about 10 seconds and a transfer was made sending the available money I had on the wallet to another wallet,” wrote one victim of today’s crypto-cash heist.
“I have no idea what happened. I barely download things and thought I was careful enough at least to avoid problems.”
BGP hijacking is, sadly, decades old, and has proven a reliable technique for criminals and other scumbags over the years.
In this case, it is thought the thieves used a compromised Equinix-hosted server in Chicago to capture traffic rerouted from AWS’s Route 53 DNS service. Technically, the miscreants behind the hijacking could have snatched control of all sites using Route 53 for DNS. The impact of the hijacking could have been a lot worse than a raid on ETH money stores.
The malicious phishing site was hosted in Russia. The only indication something was amiss was the self-signed certificate the phishing page presented, when people tried to connect to MyEtherWallet.com.
It is claimed the network block AS10297, belonging to Ohio-based website hosting biz eNet, announced it could take over traffic destined for some of AWS’s IP addresses. eNet peers with big-name carriers Level 3, Hurricane Electric, Cogent, NTT and others, and is therefore plugged into the internet’s backbone. eNet was well placed to alter part of the world’s internet plumbing to redirect connections to Route 53’s DNS service, in other words.
It’s highly likely someone took eNet’s systems on a joyride – ie: without permission – to make this routing adjustment announcement.
The attack is now believed to have been addressed, with the routes restored, although some DNS caches may still hold the wrong IP addresses for Myetherwallet.com for a while. The site is advising customers to use caution and, if possible, keep their wallets offline. The website is also advising punters to switch their DNS settings from Google’s DNS servers to those of Cloudflare, which seemed to have ignored today’s switcheroo.
This is not the first time MEW has been targetted and it definitely won’t be the last, it’s a fairly high-profit target as this attack as shown – so we will see more focused attacks on it in the future.
The crypto space is the wild wild west right now as it goes, one of the downsides of decentralization is that everyone is control of their own private keys and thus funds, opening them up to all kinds of scams, phishing attacks and DNS attacks like this one.
It will get better as the space matures, but if you’re in the space – make sure your opsec is solid.
Source: The Register
