OWASP ZSC is an open source obfuscated code generator tool in Python which lets you generate customized shellcodes and convert scripts to an obfuscated script.
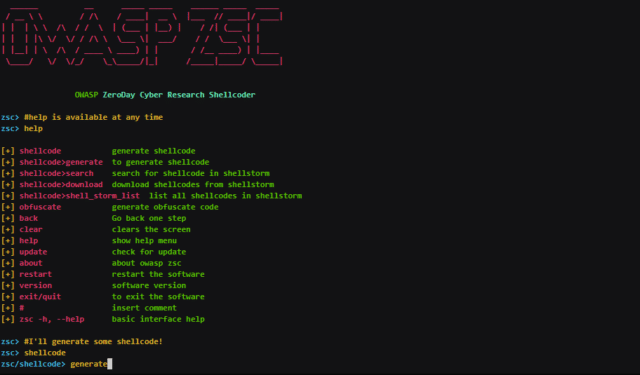
Shellcodes are small codes in Assembly language which could be used as the payload in software exploitation. Other usages are in malware, bypassing antivirus software, obfuscating code for protection and so on.
This software can be run on Windows/Linux/OSX under Python.
Why use OWASP ZSC Obfuscated Code Generator Tool
Another good reason for obfuscating files or generating shellcode with ZSC is that it can be used for pen-testing assignments. Malicious hackers use these techniques to bypass anti-virus and load malicious files in systems they have hacked using customized shellcode generators. Anti-virus tend to utilise signatures in order to identify harmful files. When using very well known encoders such as msfvenom, files generated by this program might be already flagged by anti-virus programs.
According to other shellcode generators same as Metasploit tools etc, OWASP ZSC using new encodes and methods which antiviruses won’t detect. OWASP ZSC encoders are able to generate shell codes with random encodes and that allows you to generate thousands of new dynamic shellcodes with the same job in just a second, that means, you will not get the same code if you use random encodes with same commands.
There is also this tool to check out:
– Carbylamine – A PHP Script Encoder to ‘Obfuscate/Encode’ PHP Files
You can download OWASP ZSC here:
Or read more here.

rene says
Nice article,
1 remark:
I think that the reference url in
Or read more here.
is incorrect as it points to:
http://obfuscated%20code%20generator/
and it should point to something like:
https://www.owasp.org
Darknet says
You’re absolutely right, thanks – have fixed the link!