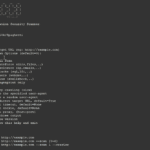
Spaghetti is an Open-source Web Application Security Scanner, it is designed to find various default and insecure files, configurations, and misconfigurations. It is built on Python 2.7 and can run on any platform which has a Python environment. Features of Spaghetti Web Application Security Scanner Fingerprints Server Web Frameworks (CakePHP, CherryPy,…) Web Application Firewall (Waf) […]
Archives for October 2017
Taringa Hack – 27 Million User Records Leaked
The Taringa hack is actually one of the biggest leaks of the year with 27 million weakly hashed passwords breached, but it’s not often covered in the Western media with it being a Latin American site (something like Reddit). The leak happened in August and it seems like the hackers were able to brute force […]
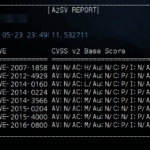
A2SV – Auto Scanning SSL Vulnerability Tool For Poodle & Heartbleed
A2SV is a Python-based SSL Vulnerability focused tool that allows for auto-scanning and detection of the common and well-known SSL Vulnerabilities. SSL Vulnerabilities Detected by A2SV [CVE-2007-1858] Anonymous Cipher [CVE-2012-4929] CRIME(SPDY) [CVE-2014-0160] CCS Injection [CVE-2014-0224] HeartBleed [CVE-2014-3566] SSLv3 POODLE [CVE-2015-0204] FREAK Attack [CVE-2015-4000] LOGJAM Attack [CVE-2016-0800] SSLv2 DROWN Planned for future: [PLAN] SSL ACCF [PLAN] […]
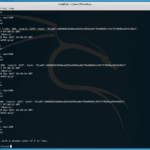
VHostScan – Virtual Host Scanner With Alias & Catch-All Detection
VHostScan is a Python-based virtual host scanner that can be used with pivot tools, detect catch-all scenarios, aliases and dynamic default pages. Features of VHostScan Virtual Host Scanner Quickly highlight unique content in catch-all scenarios Locate the outliers in catch-all scenarios where results have dynamic content on the page (such as the time) Identify aliases […]
Equifax Hack Blamed On Single Employee
We wrote about the Equifax Hack, Data Breach and Leak last month, which happened due to a flaw in Apache Struts that for some reason hadn’t been patched. Now it seems the CEO Rick Smith is basically placing the blame on a single employee that failed to pass a message on to the right people, […]