dirsearch is a Python-based command-line website directory scanner designed to brute force site structure including directories and files in websites. dirsearch Website Directory Scanner Features dirsearch supports the following: Multithreaded Keep alive connections Support for multiple extensions (-e|–extensions asp,php) Reporting (plain text, JSON) Heuristically detects invalid web pages Recursive brute forcing HTTP proxy support User […]
Archives for October 2017
XXE Injection Attacks – XML External Entity Vulnerability With Examples
XXE Injection Attacks or XML External Entity vulnerabilities are a specific type of Server Side Request Forgery or SSRF attack relating to abusing features within XML parsers. The features these attacks go after are widely available but rarely used and when trigged can cause a DoS (Denial of Service) attack and in some cases much […]
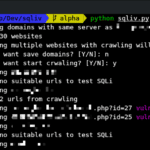
SQLiv – SQL Injection Dork Scanning Tool
SQLiv is a Python-based massive SQL Injection dork scanning tool which uses Google, Bing or Yahoo for targetted scanning, multiple-domain scanning or reverse domain scanning. SQLiv Massive SQL Injection Scanner Features Both the SQLi scanning and domain info checking are done in a multiprocess manner so the script is super fast at scanning a lot […]
OSSIM Download – Open Source SIEM Tools & Software
OSSIM is a popular Open Source SIEM or Security Information and Event Management (SIEM) product, providing event collection, normalization and correlation. OSSIM stands for Open Source Security Information Management, it was launched in 2003 by security engineers because of the lack of available open source products, OSSIM was created specifically to address the reality many […]
What You Need To Know About KRACK WPA2 Wi-Fi Attack
The Internet has been blowing up in the past week about the KRACK WPA2 attack that is extremely widespread and is a flaw in the Wi-Fi standard itself, not the implementation. It’s a flaw in the 4 way handshake for WP2 compromised by a Key Reinstallation Attack. This means any device that has correctly implemented […]