FIR (Fast Incident Response) is a cyber security incident management platform designed for agility and speed. It allows for easy creation, tracking, and reporting of cybersecurity incidents.
In the fields of computer security and information technology, computer security incident management involves the monitoring and detection of security events on a computer or computer network, and the execution of proper responses to those events. Computer security incident management is a specialized form of incident management, the primary purpose of which is the development of a well understood and predictable response to damaging events and computer intrusions.
Source: Wikipedia
FIR is for anyone needing to track cyber security incidents (CSIRTs, CERTs, SOCs, etc.). It’s was tailored to suit our needs and our team’s habits, but we put a great deal of effort into making it as generic as possible before releasing it so that other teams around the world may also use it and customize it as they see fit.
You can also check out Fully Integrated Defense Operation (FIDO) – Automated Incident Response and FastIR Collector – Windows Incident Response Tool.
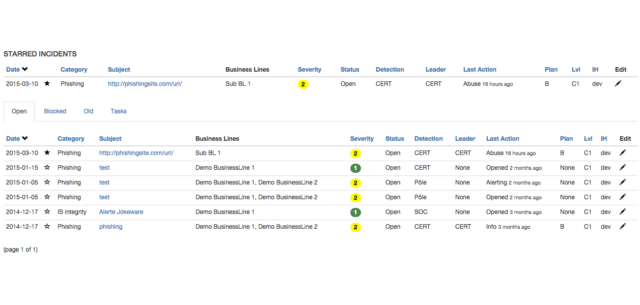
FIR Cyber Security Incident Management Features
Here are the available fields:
- Subject: short description of your incident. The one that will appear on event tables.
- Business Lines: entities concerned by this incident. You choose what you make of business lines: internal department, customers, etc.
- Category: category of the incident (ex: phishing, malware). Categories are also customizable in the admin panel.
- Status: can take three values: Open, Closed and Blocked. These are all labels defined in the admin panel
- Detection: how the incident was detected. Default values: CERT, External, Poleand Group. These values can be changed in the admin panel in the labels section
- Severity: from 1 to 4.
- Date / Time: date and time of the incident
- Is an incident: differentiates between an event and an incident
- Description: free-form text describing the event
When you are dealing with cybersecurity incident management, the following additional fields are available. These fields are only used for display and statistics:
- Actor: who is the leader on this incident management? Default values are CERT and Entity
- Plan: what is the named remediation plan used?
- Confidentiality: from C0 to C3
You can download FIR for cyber security incident management here:
Or read more here.
