Powerfuzzer is a highly automated and fully customizable web fuzzer (HTTP protocol based application fuzzer) based on many other Open Source fuzzers available and information gathered from numerous security resources and websites.
It was designed to be user-friendly, modern, effective and to work consistently.
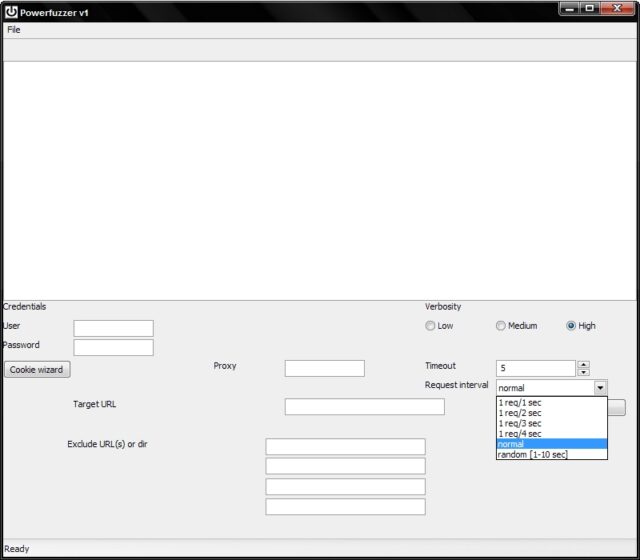
It is also designed and coded to be modular and extendable, adding new checks should simply entail adding new methods.
It’s based on tools such as cfuzzer, fuzzled, fuzzer.pl, jbrofuzz, webscarab, wapiti, Socket Fuzzer and more.
Features
Currently, it is capable of identifying these problems:
- Cross Site Scripting (XSS)
- Injections (SQL, LDAP, Code, Commands and XPATH)
- CRLF
- HTTP 500 statuses (usually indicative of a possible misconfiguration/security flaw incl. buffer overflow)
You can download Powerfuzzer here:
powerfuzzer_v1_beta_patched_binary_installer_complete.exe
Or read more here.

carlos says
what is this for?
Darknet says
Fuzzing..