Termineter is a Python Smart Meter Security Testing framework which allows authorised individuals to test Smart Meters for vulnerabilities such as energy consumption fraud, network hijacking, and more.
Many of these vulnerabilities have been highlighted by the media and advisories have been sent out by law enforcement agencies. The goal of a public release for this utility is to promote security awareness for Smart Meters and provide a tool that brings basic testing capabilities to the community and meter manufacturers so that security can be improved.
Power companies can use the framework to identify and validate internal flaws that leave them susceptible to fraud and significant vulnerabilities.
How it Works
Terminter utilises the C1218 and C1219 protocols for communication over an optical interface. Currently supported are Meters using C1219-2007 with 7-bit character sets.
This is the most common configuration found in North America. Termineter communicates with Smart Meters via a connection using an ANSI type-2 optical probe with a serial interface.
Users must have general knowledge of the meter’s internal workings in order to use Termineter proficiently.
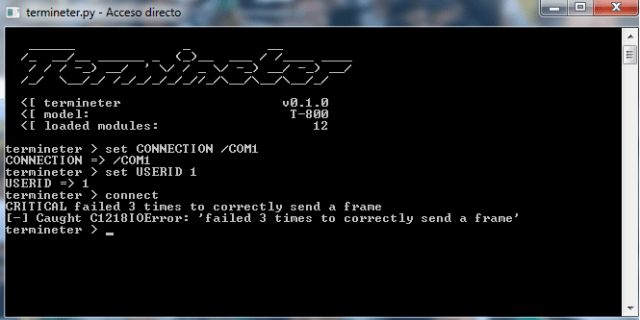
Usage
|
1 2 3 4 5 6 7 8 |
termineter [-h] [-v] [-L {DEBUG,INFO,WARNING,ERROR,CRITICAL}] [-r RESOURCE_FILE] -h, --help show this help message and exit -v, --version show program's version number and exit -L {DEBUG,INFO,WARNING,ERROR,CRITICAL}, --log {DEBUG,INFO,WARNING,ERROR,CRITICAL} set the logging level -r RESOURCE_FILE, --rc-file RESOURCE_FILE execute a resource file |
Modules
- brute_force_login – Brute Force Credentials
- dump_tables – Dump Readable C12.19 Tables From The Device To A CSV File
- enum_tables – Enumerate Readable C12.19 Tables From The Device
- get_info – Get Basic Meter Information By Reading Tables
- get_log_info – Get Information About The Meter’s Logs
- get_modem_info – Get Information About The Integrated Modem
- get_security_info – Get Information About The Meter’s Access Control
- read_table – Read Data From A C12.19 Table
- run_procedure – Initiate A Custom Procedure
- set_meter_id – Set The Meter’s I.D.
- set_meter_mode – Change the Meter’s Operating Mode
- write_table – Write Data To A C12.19 Table
You can download Termineter here:
Or you can read more here.

Mike says
This has been around since July 2012. Why profile it now? Has anything changed significantly with the tool?
Darknet says
Never written about it before.