ShellNoob is a Python-based Shellcode writing toolkit which removes the boring and error-prone manual parts from creating your own shellcodes.
Do note this is not a shellcode generator or intended to replace Metasploit’s shellcode generator, it’s designed to automate the manual parts of shellcode creation like format conversion, compilation and testing, dealing with syscalls and constants and so on.
Features
- Convert shellcode between different formats and sources. Formats currently supported: asm, bin, hex, obj, exe, C, python, ruby, pretty, safeasm, completec, shellstorm.
- Interactive asm-to-opcode conversion (and viceversa) mode. This is useful when you cannot use specific bytes in the shellcode.
- Support for both ATT & Intel syntax. Check the –intel switch.
- Support for 32 and 64 bits (when playing on x86_64 machine). Check the –64 switch.
- Resolve syscall numbers, constants, and error numbers (now implemented for real! :-)).
- Portable and easily deployable (it only relies on gcc/as/objdump and python).
- It is just one self-contained python script, and it supports both Python2.7+ and Python3+.
- In-place development: you run ShellNoob directly on the target architecture!
- Built-in support for Linux/x86, Linux/x86_64, Linux/ARM, FreeBSD/x86, FreeBSD/x86_64.
- “Prepend breakpoint” option. Check the -c switch.
- Read from stdin / write to stdout support (use “-” as filename)
- Uber cheap debugging: check the –to-strace and –to-gdb option!
- Use ShellNoob as a Python module in your scripts! Check the “ShellNoob as a library” section.
- Verbose mode shows the low-level steps of the conversion: useful to debug / understand / learn!
- Extra plugins: binary patching made easy with the –file-patch, –vm-patch, –fork-nopper options! (all details below)
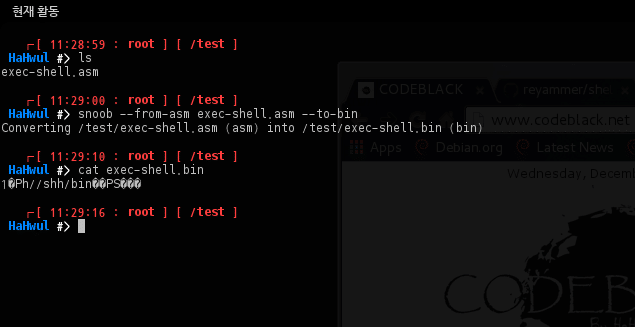
Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 |
$ ./shellnoob.py -h shellnoob.py [--from-INPUT] (input_file_path | - ) [--to-OUTPUT] [output_file_path | - ] shellnoob.py -c (prepend a breakpoint (Warning: only few platforms/OS are supported!) shellnoob.py --64 (64 bits mode, default: 32 bits) shellnoob.py --intel (intel syntax mode, default: att) shellnoob.py -q (quite mode) shellnoob.py -v (or -vv, -vvv) shellnoob.py --to-strace (compiles it & run strace) shellnoob.py --to-gdb (compiles it & run gdb & set breakpoint on entrypoint) Standalone "plugins" shellnoob.py -i [--to-asm | --to-opcode ] (for interactive mode) shellnoob.py --get-const <const> shellnoob.py --get-sysnum <sysnum> shellnoob.py --get-errno <errno> shellnoob.py --file-patch <exe_fp> <file_offset> <data> (in hex). (Warning: tested only on x86/x86_64) shellnoob.py --vm-patch <exe_fp> <vm_address> <data> (in hex). (Warning: tested only on x86/x86_64) shellnoob.py --fork-nopper <exe_fp> (this nops out the calls to fork(). Warning: tested only on x86/x86_64) "Installation" shellnoob.py --install [--force] (this just copies the script in a convinient position) shellnoob.py --uninstall [--force] Supported INPUT format: asm, obj, bin, hex, c, shellstorm Supported OUTPUT format: asm, obj, exe, bin, hex, c, completec, python, bash, ruby, pretty, safeasm All combinations from INPUT to OUTPUT are supported! |
You can download ShellNoob here:
Or read more here.
