It’s a pretty simple hack (in a rather grey-hat fashion), but it’s getting a LOT of media coverage and 160,000 network printers hacked just goes to show once again the whole Internet of Things chapter we are entering is pretty scary.
Definitely a neat hack tho, utilising the mass scanning power of Zmap and scanning for TCP Port 9100 – the port for the “RAW” print protocol. Then coding up a small C binary to send the ASCII art directly to the print spooler.
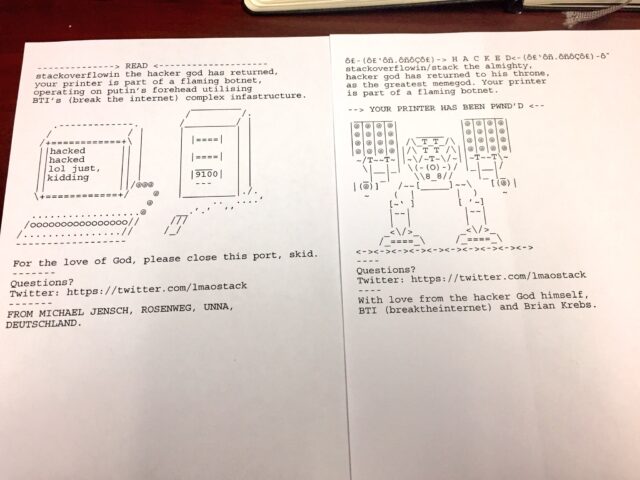
Printers around the world have been hacked and instructed to churn out pages and even sales receipts of alarming ASCII art.
The messages, which began spewing from internet-connected printers on Thursday, read: “Hacked. Stackoverflowin/stack the almighty, hacker god has returned to his throne, as the greatest memegod. Your printer is part of a flaming botnet. Your printer has been pwn’d.”
The miscreant claiming responsibility, Stackoverflowin, boasts to have hijacked more than 160,000 printers from across the internet and commanded them to emit pages of ASCII art. It appears the hacked devices range from office printers to sales terminals.
“It was kind of on impulse,” Stack told The Register. “I had been looking into printers for a while prior to this, about a few months before. I saw multiple articles about printers and it invoked my curiosity again, and yeah, it went from there.”
Stackoverflowin claims to be under 18, although a Twitter account named in the printouts describes a 23-year-old white-hat security enthusiast and embedded systems engineer. We’re told that Twitter bio is simply made up.
The hijacker says he or she wrote a script that scanned for insecure public-facing devices with open RAW, Internet Printing Protocol, and Line Printer Remote services – running on network ports 9100, 631, and 515, respectively – and fired over print jobs. This is, admittedly, trivial to do, and you can find plenty of potentially vulnerable machines on the web via Shodan.io. The search engine shows there are, right now, about 143,000 devices on the public internet with port 9100 open.
Let us be glad for once this was not a malicious hack and these printers weren’t turning into DDoS spewing botnet zombies.
The scary part of is many of these printers can have their firmware updated remotely, without any type of code signing being required. What could happen there, I will leave to your imagination.
The kid also claims to have exploited remote-code execution (RCE) vulnerabilities in the web interface built into internet-connected Xerox products to commandeer more printers. “The RCEs are undisclosed – pretty much zero-days, but I don’t like to throw that word around that much. There’s three of them in total,” Stackoverflowin said.
The first printouts had a simple message accusing people of wasting paper, and included a Protonmail email address that has been since disabled. Those messages were more of a test, Stackoverflowin explained: “I was just debugging a segfault, my code was crashing at around 50,000 devices for some reason.”
A second surge of printouts came in two forms: one with ASCII art of a computer, and the other with a robot. On the computer version, the printer’s administrators are urged to firewall off their devices from the public internet.
Judging from photos cropping up on social networks, printers around the world really were hit by Stackoverflowin, who said it was somewhat dispiriting how easy this hack was.
“I used zmap to get the IPs with the targeted ports then a small ‘loader’ that I coded in C to actually do the print job and send the packet,” Stack told us. “With most of these printers you can push your own firmware to them – the firmware doesn’t need to be signed.”
Sending over print jobs is one thing. If any of these holes can be exploited to achieve remote-code execution on the printer, these vulnerabilities can be used to build a Mirai-style botnet and cause havoc online. Although Stack’s printer spam mentions devices joining a “flaming botnet,” we’re told no such network was formed – it was a hypothetical threat, apparently.
Overall it’s a pretty impressive hack, with this kid getting 160,000 printers to work, my Mom can’t even get 1 to work most of the time.
And I’m absolutely sure we’ll be seeing many more of these random commodity devices with network interfaces, connected to the Internet being hacked in the coming year.
Source: The Register
