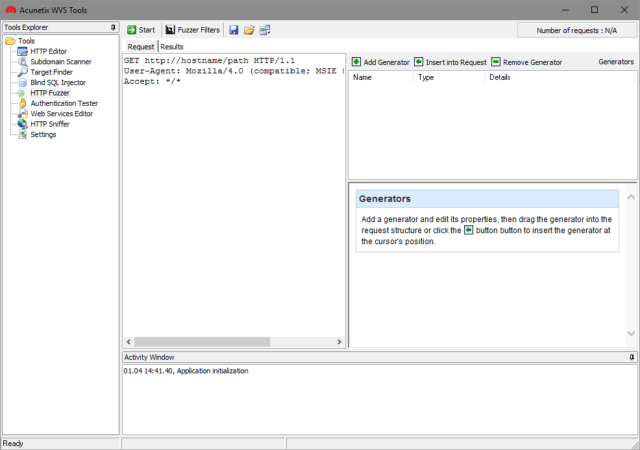
Not long after releasing v11 of their scanner, Acunetix has decided to deliver free manual pen-testing tools. Previously these tools were only available to paying Acunetix customers, now anyone can use them to make their manual web application testing easier.
Penetration testers can make use of an HTTP Editor to modify or craft HTTP requests and analyse responses; intercept and modify HTTP traffic on the fly using the integrated HTTP Sniffer; fuzz test HTTP requests using the HTTP Fuzzer and test Blind SQL Injection vulnerabilities further using the Blind SQL Injector, among others.
The Tools
- HTTP Editor: Allows you to create, analyze and edit client HTTP requests; as well as inspect server responses. It also includes an encoding and decoding tool to encode/decode text and URL’s to MD5 hashes, UTF-7 and other formats.
- HTTP Sniffer: A proxy that allows you to analyse HTTP requests and responses, and edit these while they are in transit. The HTTP sniffer can also be used to manually crawl a site, and use the manual crawl to seed an Acunetix scan.
- HTTP Fuzzer: A tool which allows you to automatically send a large number of HTTP requests including invalid, unexpected and random data to a website, to test input validation and handling of invalid data by the web application.
- Blind SQL Injector: An automated database data exfiltration tool. By using Blind SQL injection vulnerabilities discovered when scanning a website, it is possible to demonstrate the serious impact a Blind SQL injection vulnerability can have on the website. Used to enumerate databases, tables, fields and dump data from the vulnerable web application.
- Subdomain Scanner: Scans a top-level domain to discover subdomains configured in its hierarchy, by using the target domain’s DNS server, or any other DNS server specified by the user. While scanning, this tool will also automatically identify and inform the user if the domain being scanned is using some kind of wildcard characters, such as *.domain.com.
- Target Finder: An IP range / port scanner which can be used to discover running web servers on a given IP or within a specified range of IPs. The list of ports on which the web servers are listening can also be configured. The default ports the scanner will scan are port 80 for HTTP and port 443 for SSL.
- Authentication Tester: Used to test the strength of both usernames and passwords within HTTP and web forms authentication environments via a dictionary attack.
There are also detailed documents with examples for:
You can download the tools here:
Acunetix Free Manual Pen Testing Tools
You can read more here:
