Barnyard2 is an open source dedicated spooler for Snort output as unified2 binary output files. Its primary use is allowing Snort to write to disk in an efficient manner and leaving the task of parsing binary data into various formats to a separate process that will not cause Snort to miss network traffic.
How it Works
Barnyard2 has 3 modes of operation:
- batch (or one-shot),
- continual, and
- continual w/ bookmark.
In batch (or one-shot) mode, barnyard2 will process the explicitly specified file(s) and exit.
In continual mode, barnyard2 will start with a location to look and a specified file pattern and continue to process new data (and new spool files) as they appear.
Continual mode w/ bookmarking will also use a checkpoint file (or waldo file in the snort world) to track where it is. In the event, the barnyard2 process ends while a waldo file is in use, barnyard2 will resume processing at the last entry as listed in the waldo file.
Barnyard2 processing is controlled by two main types of directives: input processors and output plugins. The input processors read information in from a specific format ( currently the spo_unified2 output module of Snort) and output them in one of several ways.
Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 |
barnyard2 [-options] Gernal Options: -c <file> Use configuration file <file> -C <file> Read the classification map from <file> -D Run barnyard2 in background (daemon) mode -e Display the second layer header info -E Log alert messages to NT Eventlog. (Win32 only) -F Turn off fflush() calls after binary log writes -g <gname> Run barnyard2 gid as <gname> group (or gid) after initialization -G <file> Read the gen-msg map from <file> -h <name> Define the hostname <name>. For logging purposes only -i <if> Define the interface <if>. For logging purposes only -I Add Interface name to alert output -l <ld> Log to directory <ld> -m <umask> Set umask = <umask> -O Obfuscate the logged IP addresses -q Quiet. Don't show banner and status report -r <id> Include 'id' in barnyard2_intf<id>.pid file name -R <file> Read the reference map from <file> -S <file> Read the sid-msg map from <file> -t <dir> Chroots process to <dir> after initialization -T Test and report on the current barnyard2 configuration -u <uname> Run barnyard2 uid as <uname> user (or uid) after initialization -U Use UTC for timestamps -v Be verbose -V Show version number -? Show this information Continual Processing Options: -a <dir> Archive processed files to <dir> -f <base> Use <base> as the base filename pattern -d <dir> Spool files from <dir> -n Only process new events -w <file> Enable bookmarking using <file> Batch Processing Mode Options: -o Enable batch processing mode |
Examples
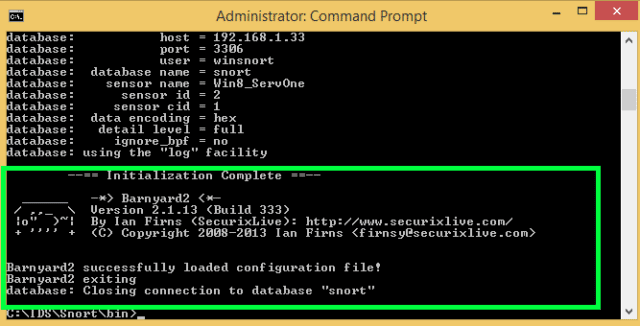
1. Using barnyard2 in continuous mode with a waldo file
|
1 |
# ./barnyard2 -c /etc/barnyard2.conf -d /var/snort -f snort.u2 -w /var/snort/snort.waldo |
2. Using barnyard2 in batch mode
|
1 |
# ./barnyard2 -c /etc/barnyard2.conf -o file1.u2 file2.u2 file3.u2 |
You can download Barnyard2 here:
Or read more here.
