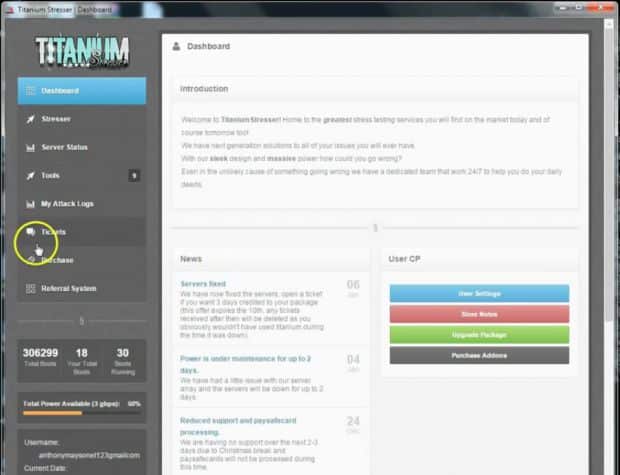
Another DDoS service down after the owner got busted, this time a UK teenager who created the service called Titanium Stresser when he was just 15.
Not long ago we wrote about the two Israeli guys who got busted for running the VDoS-s.com DDoS Service.
There seems to be a bit of a crack down on such things going on, but with Mirai Source Code out there now – I don’t think they are going after the right targets.
A 19 year-old Hertfordshire man has pled guilty to running the Titanium Stresser booter service that offered distributed denial of service (DDoS)-as-a-service.
Such services are often marketed as innocuous and legitimate stress testing tools, but are instead often used for cheap and effective attacks of websites. Prosecutors say Adam Mudd earned more than US$385,000 (£315,000 A$505,000) by renting out the service he created as a 15 year-old.
He pled guilty at London’s Old Bailey to two offences under the Computer Misuse Act and one money laundering offence and will be sentenced in December. Bedfordshire Police say in a notice that Mudd’s now dead Titanium Stresser was used in many thousands of DDoS attacks by criminals renting the service.
Mudd is accused of committing 594 DDoS attacks against 181 targets between December 2013 and March last year. His platform became one of the most popular such services, even offering free 60-second DDoS attacks.
That’s a lot of money for someone who isn’t even 20 yet, he’s clearly very smart so I’m hoping he doesn’t go to jail for too long and get turned into a hardcore criminal.
He should come out and use his talents for something useful and build a legitimate career.
Mudd’s work would become the basis of the Lizard Stresser, another for-hire DDoS tool by boastful hacking group Lizard Squad, most famously used to take down the Xbox Live and Playstation networks over the 2014 festive break.
Police were able to nail Mudd thanks in part to his keeping of DDoS attack logs. Detective inspector Martin Peters of the Eastern Region Special Operations cyber crime unit says the case is regrettable due to Mudd’s misuse of talent.
“Adam Mudd’s case is a regrettable one, because this young man clearly has a lot of skill, but he has been utilising that talent for personal gain at the expense of others,” Peters says.
“We want to make clear it is not our wish to unnecessarily criminalise young people, but want to harness those skills before they accelerate into crime.”
Detective Peters says the investigation was complex with DDoS customers around the globe.
We will have to wait and see what the sentence will be like as this isn’t exactly a common charge, they can be a heavy handed sometimes though as they like to make an example when they do somehow manage to catch a cyber-criminal (as it’s not very often..).
Honestly DDoS services are probably one of my least favourite things (having been on the recieving end of a few) – that much fire-power should not be commoditised for a few dollars when taking a website down for a few hours can hurt a business really seriously.
Source: The Register
