Pulled Pork is a PERL based tool for Suricata and Snort rule management – it can determine your version of Snort and automatically download the latest rules for you.
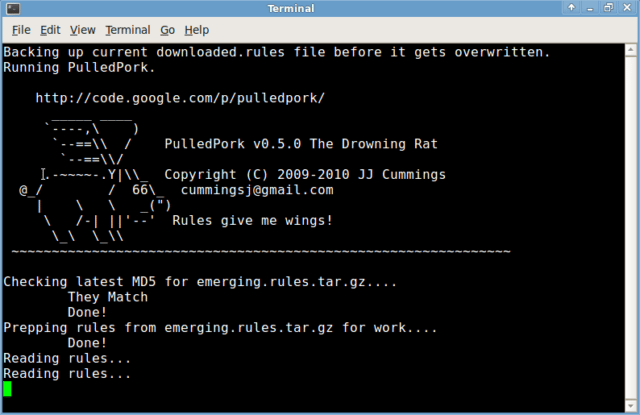
The name was chosen because simply speaking, it Pulls the rules. Using a regular crontab you can keep your Snort or Suricata rules up to date automatically.
Features and Capabilities
Pulledpork 0.7.2 has been tested and works with Snort 2.9.8.3/Suricata 3.1.3 and the Snort Registered rules/ETOpen/ETPro rulesets.
- Automated downloading, parsing, state modification and rule modification for all of your snort rulesets.
- Checksum verification for all major rule downloads
- Automatic generation of updated sid-msg.map file
- Capability to include your local.rules in sid-msg.map file
- Capability to pull rules tarballs from custom urls
- Complete Shared Object support
- Complete IP Reputation List support
- Capability to download multiple disparate rulesets at once
- Maintains accurate changelog
- Capability to HUP processes after rules download and process
- Aids in tuning of rulesets
- Verbose output so that you know EXACTLY what is happening
- Minimal Perl Module dependencies
- Support for Suricata, and ETOpen/ETPro rulesets
Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 |
Usage: ./pulledpork.pl [-dEgHklnRTPVvv? -help] -c <config filename> -o <rule output path> -O <oinkcode> -s <so_rule output directory> -D <Distro> -S <SnortVer> -p <path to your snort binary> -C <path to your snort.conf> -t <sostub output path> -h <changelog path> -I (security|connectivity|balanced) -i <path to disablesid.conf> -b <path to dropsid.conf> -e <path to enablesid.conf> -M <path to modifysid.conf> -r <path to docs folder> -K <directory for separate rules files> Options: -help/? Print this help info. -b Where the dropsid config file lives. -C Path to your snort.conf -c Where the pulledpork config file lives. -d Do not verify signature of rules tarball, i.e. downloading fron non VRT or ET locations. -D What Distro are you running on, for the so_rules Valid Distro Types: Debian-6-0, Ubuntu-10-4, Ubuntu-12-04, Centos-5-4 FC-12, FC-14, RHEL-5-5, RHEL-6-0 FreeBSD-8-1, FreeBSD-9-0, FreeBSD-10-0, OpenBSD-5-2, OpenBSD-5-3 OpenSUSE-11-4, OpenSUSE-12-1, Slackware-13-1 -e Where the enablesid config file lives. -E Write ONLY the enabled rules to the output files. -g grabonly (download tarball rule file(s) and do NOT process) -h path to the sid_changelog if you want to keep one? -H Send a SIGHUP to the pids listed in the config file -I Specify a base ruleset( -I security,connectivity,or balanced, see README.RULESET) -i Where the disablesid config file lives. -k Keep the rules in separate files (using same file names as found when reading) -K Where (what directory) do you want me to put the separate rules files? -l Log Important Info to Syslog (Errors, Successful run etc, all items logged as WARN or higher) -L Where do you want me to read your local.rules for inclusion in sid-msg.map -m where do you want me to put the sid-msg.map file? -M where the modifysid config file lives. -n Do everything other than download of new files (disablesid, etc) -o Where do you want me to put generic rules file? -p Path to your Snort binary -P Process rules even if no new rules were downloaded -R When processing enablesid, return the rules to their ORIGINAL state -r Where do you want me to put the reference docs (xxxx.txt) -S What version of snort are you using -s Where do you want me to put the so_rules? -T Process text based rules files only, i.e. DO NOT process so_rules -u Where do you want me to pull the rules tarball from ** E.g., ET, Snort.org. See pulledpork config rule_url option for value ideas -V Print Version and exit -v Verbose mode, you know.. for troubleshooting and such nonsense. -vv EXTRA Verbose mode, you know.. for in-depth troubleshooting and other such nonsense. -w Skip the SSL verification (if there are issues pulling down rule files) -W Where you want to work around the issue where some implementations of LWP do not work with pulledpork's proxy configuration. |
You can download Pulled Pork here:
Or read more here.
