Nishang is a framework and collection of scripts and payloads which enables usage of PowerShell for penetration testing, offensive security and red teaming. Nishang is useful during all phases of penetration testing.
Usage
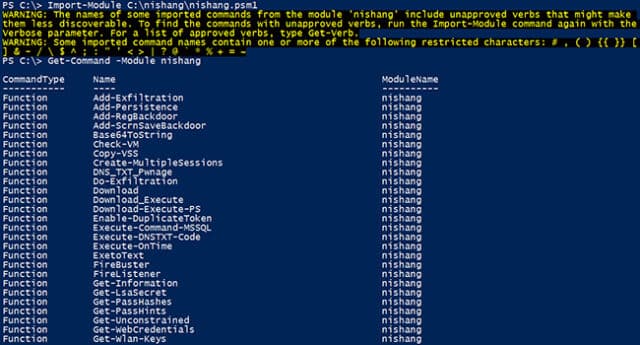
Import all the scripts in the current PowerShell session (PowerShell v3 onwards).
|
1 |
PS C:\nishang> Import-Module .\nishang.psm1 |
Use the individual scripts with dot sourcing.
|
1 2 3 |
PS C:\nishang> . C:\nishang\Gather\Get-Information.ps1 PS C:\nishang> Get-Information |
To get help about any script or function, use:
|
1 |
PS C:\nishang> Get-Help [scriptname] -full |
Note that the help is available for the function loaded after running the script and not the script itself since version 0.3.8. In all cases, the function name is same as the script name.
For example, to see the help about Get-WLAN-Keys.ps1, use
|
1 2 3 |
PS C:\nishang> . C:\nishang\Get-WLAN-Keys.ps1 PS C:\nishang> Get-Help Get-WLAN-Keys -Full |
Scripts
Nishang comes with a myriad of scripts divided into various categories:
- ActiveDirectory
- Backdoors
- Clients
- Escalation
- Execution
- Gathering
- MiTM
- Pivoting
- Scanning
- Powerpreter
- Shells
- Utilities
You can download Nishang here:
Or read more here.
