mitmproxy is an interactive TLS-capable intercepting HTTP proxy for penetration testers and software developers.
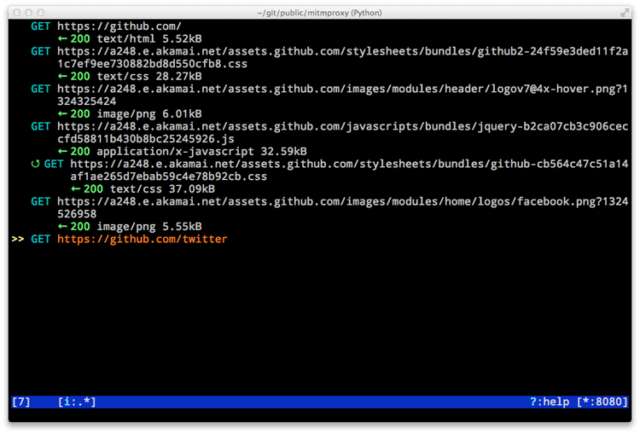
It’s a console tool that allows interactive examination and modification of HTTP traffic. It differs from mitmdump in that all flows are kept in memory, which means that it’s intended for taking and manipulating small-ish samples.
The command-line companion called mitmdump provides tcpdump-like functionality to let you view, record, and programmatically transform HTTP traffic.
Features
- Intercept HTTP requests and responses and modify them on the fly.
- Save complete HTTP conversations for later replay and analysis.
- Replay the client-side of an HTTP conversations.
- Replay HTTP responses of a previously recorded server.
- Reverse proxy mode to forward traffic to a specified server.
- Transparent proxy mode on OSX and Linux.
- Make scripted changes to HTTP traffic using Python.
- SSL certificates for interception are generated on the fly.
Installation
Ubuntu comes with Python but we need to install pip, python-dev and several libraries. This was tested on a fully patched installation of Ubuntu 14.04.
|
1 2 |
sudo apt-get install python-pip python-dev libffi-dev libssl-dev libxml2-dev libxslt1-dev libjpeg8-dev zlib1g-dev sudo pip install mitmproxy |
Once installation is complete you can run mitmproxy or mitmdump from a terminal.
On Ubuntu 12.04 (and other systems with an outdated version of pip), you may need to update pip using pip install -U pip before installing mitmproxy.
You can download mitmproxy here:
Or read more here.
