DDoS or Booter services have been around for a while, but VDoS-s.com was a particularly slick (and shameless) one with a content marketing strategy and active social media accounts. Two Israeli men were arrested for running the service after ironically being hacked by a security researcher.
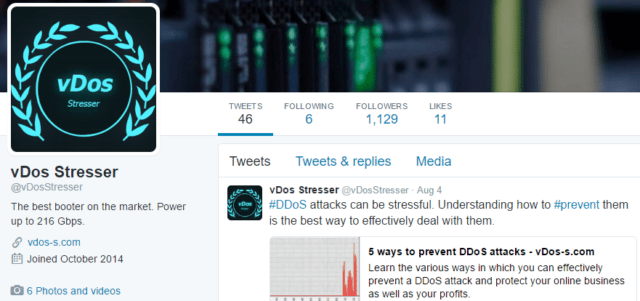
They called their service a ‘Stresser’ and claimed to have up to 216Gbps of bandwidth available (yah that’s a lot, and could take most data centers off-line).
Two Israeli men have been arrested for running a distributed-denial-of service-as-a-service site, after one seemingly claimed to attack the Pentagon.
Itay Huri and Yarden Bidani, released on US$10,000 bonds, were arrested following a tip off from the FBI, local news site TheMarker reports.
A Twitter account using Bidani’s name and handle tweeted last year that parts of the Pentagon site were down after a DDoS.
Their slick DDoS site vDos-s.com charged between US$30 and US$200 a month for DDoS attacks sold as legitimate network stress testing.
“We are not just another booter, we guarantee 10-50Gbps of UDP traffic per stress test using our DNS method, our high end dedicated servers can satisfy even the most power hungry customers,” the pair wrote on their site.
They have also allegedly cashed in over $600,000USD in the past 2 years from running the service, which is some serious coin.
Although, attacking The Pentagon DNS servers was probably a poorly conceived idea.
VDos targeted 150,000 victims according to a stolen database provided to KrebsonSecurity lifted from the site by an anonymous security researcher who exploited a vulnerability.
That database revealed the actors’ identities along with details of paying customers.
The lifted document mentions victim sites including the UK’s Imperial College Model United Nations club, game site GoodGame.co.uk, and anti-DDoS site Zare.com.
KrebsonSecurity says the booter site made some US$600,000 over the last two years.
The pair seemed to have tried to present the company as a legitimate stress testing service, rather than as guns for hire. Customers using the “legitimate stress testing company” are told they “are prohibited from stressing internet connections and/or servers that [they] do not have ownership of or authorisation to test”.
The domain is down now, and both chaps out on bail so I think the idea of them running this as a legitimate stress testing service seems ill-conceived.
It’s pretty impressive what they’ve pulled off in the info in the reports are correct which puts them at 18 years old now, and they have run this service since 2012 which made them 14 years old when they launched a fully formed money making machine (albeit rather illegal).
Source: The Register

kitsune says
RIP VDOS :(