MANA Toolkit is a set of tools for rogue access point (evilAP) attacks and wireless MiTM.
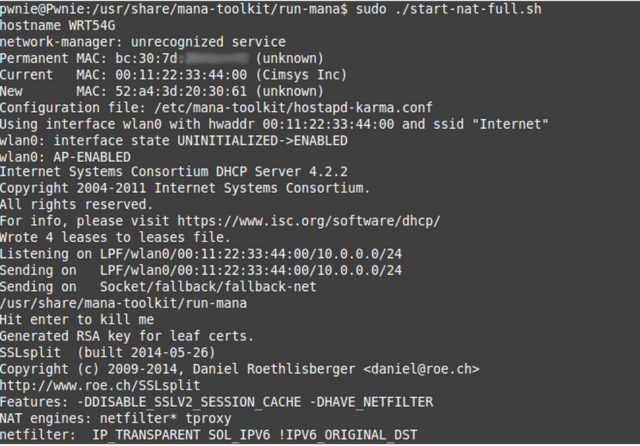
More specifically, it contains the improvements to KARMA attacks implemented into hostapd, as well as some useful configs for conducting MitM once you’ve managed to get a victim to connect.
Contents
MANA Toolkit contains:
- kali/ubuntu-install.sh – simple installers for Kali 1.0.9 and Ubuntu 14.04 (trusty)
- slides – an explanation of what we’re doing here
- run-mana – the controller scripts
- hostapd-mana – modified hostapd that implements our new mana attacks
- crackapd – a tool for offloading the cracking of EAP creds to an external tool and re-adding them to the hostapd EAP config (auto crack ‘n add)
- sslstrip-hsts – our modifications to LeonardoNVE’s & moxie’s cool tools
- apache – the apache vhosts for the noupstream hacks; deploy to /etc/apache2/ and /var/www/ respectively
Installation
The simplest way to get up and running is it “apt-get install mana-toolkit” on Kali. If you want to go manual to get the latest version, check below. Make sure to edit the start script to point to the right wifi device.
To get up and running setup a Kali box (VM or otherwise), update it, then run kali-install.sh
To get up and running setup a Ubuntu 14.04 box (VM or otherwise), update it, then run ubuntu-install.sh
If you’re installing from git, you can use the following commands after you have grabbed the necessary dependencies:
|
1 2 3 4 5 6 |
git clone --depth 1 https://github.com/sensepost/mana cd mana git submodule init git submodule update make make install |
You can download MANA Toolkit here:
Source: mana-1.3.1.zip
Binary: mana-toolkit-1.3-1debian1_amd64.deb
Or read more here.
