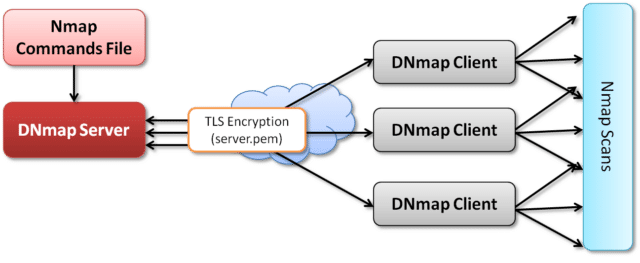
dnmap is a distributed Nmap framework which can hand off Nmap scans to several clients. It reads an already created file with Nmap commands and send those commands to each client connected to it.
The framework use a client/server architecture. The server knows what to do and the clients do it. All the logic and statistics are managed in the server. Nmap output is stored on both server and client.
Usually you would want this if you have to scan a large group of hosts and you have several different internet connections (or friends that want to help you).
Features of the framework
Clients can be run on any computer on Internet. Do not have to be local cluster or anything.
Is uses TLS protocol for encryption.
dnmap_server features
- If the server goes down, clients continue trying to connect until the server gets back online.
- If the server goes down, when you put it up again it will send commands starting from the last command given before the shutdown. You do not need to remember where it was.
- You can add new commands to the original file without having to stop the server. The server will read them automatically.
- If some client goes down, the server will remember which command it was executing and it will re-schedule it for later.
- It will store every detail of the operations in a log file.
- It shows real time statistics about the operation of each client, including:
- Number of commands executed
- Last time seen
- Uptime
- Version of the client
- If the client is being run as root or not.
- It calculates the amount of commands executed per minute
- The historic average of the amount of commands executed per minute
- The status of the client (Online, Offline, Executing or Storing)
- You can choose which port to use. Defaults to 46001
dnmap_client features
- If the server goes down, it keeps connecting to it until it’s up again.
- Strip strange characters from the command sent by the server. Tries to avoid command injection vulns.
- It only executes the Nmap command. It deletes the command send by the server and changes it by a known Nmap binary in the system.
- You can pick an alias for your user.
- You can change which port to connect to.
- If the command sent by the server does not have a -oA option, the client add it anyway to the command, so it will always have a local copy of the output.
Security
This framework is NOT intended to be secure or to be used by people you do not trust. As the client will execute any Nmap command you send, the client is trusting you. This was created so your friends can help you in the scan, or to use all your computers at the same time.
The client does not need to be run as root, but be aware that most Nmap scan types need the client to be run as root. If some of your clients are not root, you can still send them TCP connect type of scans for example. But this should be done by you in the Nmap commands file.
You can download dnmap here:
Or read more here.
