So apparently this Hijacking Unused IPv addresses has been going on for a while, but with quite a lot number of attempts recently it’s ramped up a LOT since the September announcement by ARIN about IPv4 depletion. There was only only 50 hijacking attempts between 2005 and 2015.
Since September, ARIN has already seen 25 such attacks though – which is basically 5 years worth.
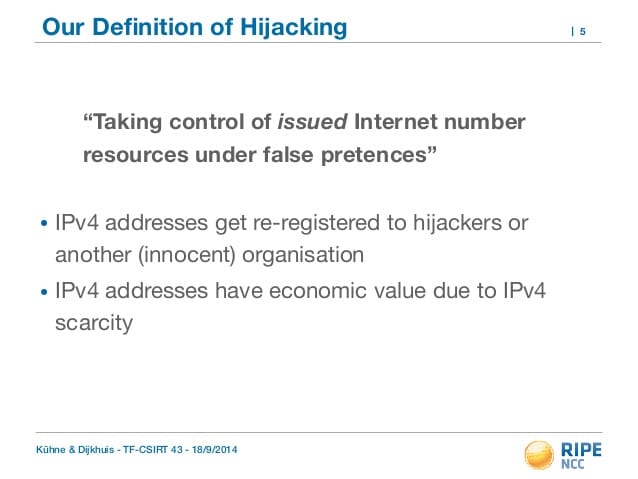
IPv4 addresses are now so valuable that criminals are setting up shell companies so they can apply for addresses, then resell them to users desperate to grow their networks.
Criminals are doing so because there are no more IPv4 addresses left: the American Registry for Internet Numbers (ARIN) ran out in September 2015.
ARIN maintains a waiting list for address buyers and also oversees a market for used IPv4 addresses. While it is conceivable that some users will hand back addresses they no longer require, the IPv4 transfer market is short of stock.
Hence criminals’ interest in ways to land themselves IP addresses, some of which were detailed this week by ARIN’s senior director of global registry knowledge, Leslie Nobile, at the North American Network Operators Group’s NANOG 67 conference.
Nobile explained that criminals look for dormant ARIN records and try to establish themselves as the rightful administrator. ARIN has 30,556 legacy network records, she said, but a validated point of contact for only 54 per cent of those networks. The remaining ~14,000 networks are ripe for targeting by hijackers who Nobile said are only interested in establishing legitimacy with ARIN so they can find a buyer for un-used IPv4 addresses possessed by dormant legacy networks.
So if you’re a company that owns a dormant IPv4 address space, give it back or sell it – because people need it! And secondly, it might get stolen anyway.
From the figures it seems there’s about 15,000 dormant network records without a validated point of contact.
Criminals do so by finding dormant ARIN records and Whois data to see if there is a valid contact, then ascertaining if IPv4 allocations are currently routed. If the assigned addresses are dark and no active administrator exists, hijackers can revive dormant domain names or even re-register the names of defunct companies in order to establish a position as legitimate administrators of an address space. If all goes well, the hijackers end up with addresses to sell.
This activity is not rampant, but is rising fast: Nobile said ARIN detected about 50 such hijacking attempts between 2005 and 2015. Since announcing IPv4 depletion in September 2015 the organisation has detected about 25.
Nobile said ARIN has also found “fraud rings … people who set up shell companies in order to hoard IPv4 address spaces.”
These fraudsters came into existence just before the depletion of the IPv4 address space. One entity created 30 shell companies with the sole intention of securing addresses for later re-sale.
“They were good,” Nobile admitted. “They got by us.”
ARIN’s tightened its checks of late to stop hijackers and fraudsters. Nobile suggested you do likewise by keeping Whois records up to date and responding to ARIN’s annual point of contact validation request.
Keep your WHOIS records up to date, especially contact details for your network blocks, even if they are in use – it will go a long way towards not getting jacked.
Same goes for domains.
Source: The Register
