IPGeoLocation is a Python based tool designed to retrieve IP geolocation information from the ip-api service, useful for building into your security tools.
Do be aware that as this tool is leveraging a 3rd party API, you will be limited to 150 requests a minute. Whilst that is quite a lot, just be wary of it because if you exceed the limit you will get blocked.
Features
- Retrieve IP or Domain Geolocation.
- Retrieve your own IP Geolocation.
- Retrieve Geolocation for IPs or Domains loaded from file. Each target in new line.
- Define your own custom User Agent string.
- Select random User-Agent strings from file. Each User Agent string in new line.
- Proxy support.
- Select random proxy from file. Each proxy URL in new line.
- Open IP geolocation in Google Maps using the default browser.
- Export results to csv, xml and txt format.
Geolocation Information Retrieved
- ASN
- City
- Country
- Country Code
- ISP
- Latitude
- Longtitude
- Organization
- Region Code
- Region Name
- Timezone
- Zip Code
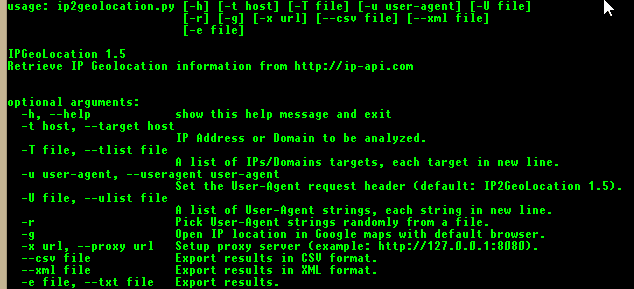
Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 |
$ ./ip2geolocation.py usage: ipgeolocation.py [-h] [-m] [-t TARGET] [-T file] [-u User-Agent] [-U file] [-g] [--noprint] [-v] [--nolog] [-x PROXY] [-X file] [-e file] [-ec file] [-ex file] IPGeolocation 2.0.3 --[ Retrieve IP Geolocation information from ip-api.com --[ Copyright (c) 2015-2016 maldevel (@maldevel) --[ ip-api.com service will automatically ban any IP addresses doing over 150 requests per minute. optional arguments: -h, --help show this help message and exit -m, --my-ip Get Geolocation info for my IP address. -t TARGET, --target TARGET IP Address or Domain to be analyzed. -T file, --tlist file A list of IPs/Domains targets, each target in new line. -u User-Agent, --user-agent User-Agent Set the User-Agent request header (default: IP2GeoLocation 2.0.3). -U file, --ulist file A list of User-Agent strings, each string in new line. -g Open IP location in Google maps with default browser. --noprint IPGeolocation will print IP Geolocation info to terminal. It is possible to tell IPGeolocation n ot to print results to terminal with this option. -v, --verbose Enable verbose output. --nolog IPGeolocation will save a .log file. It is possible to tell IPGeolocation not to save those log files with this option. -x PROXY, --proxy PROXY Setup proxy server (example: http://127.0.0.1:8080) -X file, --xlist file A list of proxies, each proxy url in new line. -e file, --txt file Export results. -ec file, --csv file Export results in CSV format. -ex file, --xml file Export results in XML format. |
You can download IPGeoLocation v2.0.3 here:
Or read more here.
