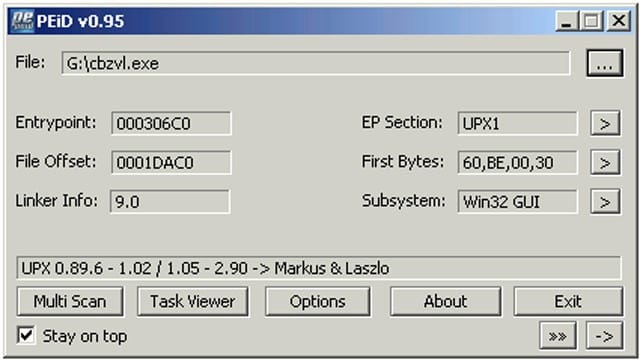
PEiD is an intuitive application that relies on its user-friendly interface to detect PE packers, cryptors and compilers found in executable files – its detection rate is higher than that of other similar tools since the app packs more than 600 different signatures in PE files.
What is PEiD?
PEiD comes with three different scanning methods, each suitable for a distinct purpose. The Normal one scans the user-specified PE file at its Entry Point for all its included signatures. The so-called Deep Mode comes with increased detection ratio since it scans the file’s Entry Point containing section, whereas the Hardcore mode scans the entire file for all the documented signatures.
When users need to get their results right away, they can rely on the Normal or the Deep modes, and they can turn to the Hardcore one when they are willing to wait the time it takes for the scan to complete – regardless of the chosen type, the generated results are as accurate as possible due to the error control method.
In addition to the intuitive interface, its functions can also be accessed via command-line, and the detailed documentation can help users get familiarized to the proper commands and parameters.
This tool also allows users to explore all the currently running processes and terminate them with a single mouse click. One can also dump a module then scan then dumped image, or analyze the dependent modules of a process.
You can also check out:
– Malware Analyser v3.0 – A Static & Dynamic Malware Analysis Tool
How to use PEiD
The best results can be obtained if each file is analysed separately as it takes less time to complete the scan, but PEiD also supports batch processing. Users can choose a folder, then set PEiD to select the PE files and scan them.
To sum it up, PEiD is a feature-packed application that can scan PE files and identify packers and compilers, while also featuring a HEX viewer and a task manager.
Update your PEiD Signatures
Update your signatures (initial file is empty). Replace the initial userdb.txt file with one of these files:
– http://handlers.sans.org/jclausing/userdb.txt
– https://raw.githubusercontent.com/ynadji/peid/master/userdb.txt
Download PEiD
You can download PEiD here:
Or read more here.
